The New Zealand Press Association reports:
The Labour Party has apologised to donors, after a right-wing blogger said he would release their personal details following what the party called a malicious breach of its website.
In an email sent to donors yesterday, party secretary Chris Flatt said an investigation was launched after the discovery of a possible breach of the online donation system.
Details taken included names, email addresses, and amounts of donations and membership fees.
Mr Flatt said the system had been secured to ensure a breach could not recur, and there would be an independent security review.
Blogger Cameron Slater said he had the data and had done nothing illegal to obtain it.
Read more on the National Business Review.
From Slater’s blog, it appears that he is saying no hack was necessary and that the Labour Party did not realize that their donors’ information was easily available on the web. Slater writes on his blog:
These donation lists have been public for months and I reject any claim that I am a thief or a bludger (Eddie/Jenny Michie, I’m not reposting your link).
Labour makes a great deal of fuss about political donations, in fact they even passed the odious Electoral Finance Act to shed sunlight upon dona tions. Like wise the Greens have made representations on electoral law reform that suggests that all donations be made public.
Accordingly in line with their previous assertions Labour has made about donors and donations, I think sunlight is the best disinfectant here and so their online donations will be published. They have been public any way for at least the three months I have been looking at them.
[…]
…. slack security means that there are hundreds of pages of names and membership details that Labour itself has published for us to examine.
It is not clear from the redacted graphic he provides whether donors’ credit card numbers were also visible to anyone who wanted to view them, and I’ve emailed the blogger to ask about that as the party’s statement makes no mention of credit card numbers being exposed.
At the time of this posting, it appears that a file with donor information was uploaded to Scribd:
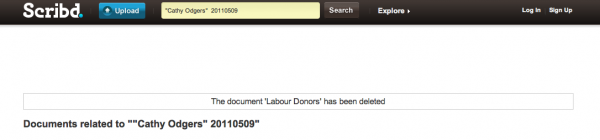
That file, however, has been removed:
Update 1: The blogger involved, Cameron Slater, responded to my inquiry by saying that credit card details were not exposed as far as he could tell. NZPA and NBR have since reported additional details on the breach, here.