Today, HHS added 37 incidents to its public breach tool, which I’ve summarized over on phiprivacy.net (here and here). But it looks like I can’t catch a break, as the Maryland Attorney General’s Office also updated its breach tool. So here are some more breaches I did not previously know about, with links to their reports to Maryland:
Next Day Blinds learned on November 4th that an unauthorized individual had entered their offices and stolen a secure safe from the premises. As a result, someone may have accessed the name,credit card number, expiration date, security code, checking account number, bank routing number, and address of 16 Maryland residents and an unspecified number of customers in other states. Notification.
The owner of Fisher’s Popcorn seems to have fallen for the “I’m a technician for Microsoft” scam. When she became suspicious after the “technician” helped her and asked for payment, she deleted all the information and disconnected her computer. Whatever she did made it impossible to determine whether there had been a security breach involving employee information, so she wound up notifying 50 employees. Notification.
Insurance giant Aetna reported that due to a vendor’s error, some of a customer’s employees going through an enrollment process were able to temporarily view the name and social security number of another employee’s beneficiary. Notification. Template letter to those affected. AllClear ID information.
Mosaic discovered that a number of their employees had fallen for a phishing scheme. The compromised email accounts contained information Mosaic used for administrative purposes, including some individuals’ names, addresses, dates of birth, Social Security numbers, and financial account information. Notification.
Colombo Bank notified customers on April 19 that they had, just that day, become aware of an incident possibly resulting in debit card information being compromised. They write, “Magnetic stripe counterfeit fraud has been identified on some MasterCard debit card accounts. This type of fraud could have resulted in the unauthorized access to your Colombo Bank Debit Card information.” Notification. FAQ.
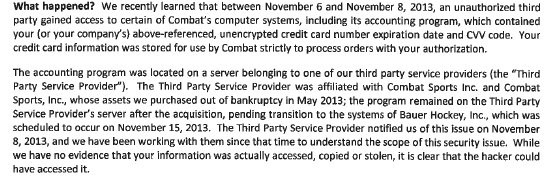
Combat Sports recently reported a breach involving BPS Diamond Sports:
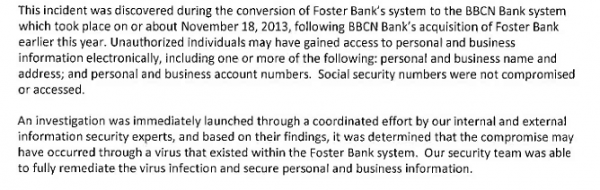
If you buy a bank, you probably don’t want its systems to come with a virus that immediately adds to breach costs. Yet that’s what seems to have happened to BBCNBank (template letter here):
 A MassMutual employee reportedly e-mailed a spread sheet with 510 Maryland residents’ information to the wrong client. Notification.
A MassMutual employee reportedly e-mailed a spread sheet with 510 Maryland residents’ information to the wrong client. Notification.
Branch Banking & Trust (BB&T) report that their security controls prevented a rogue employee from misusing customer data, but since they couldn’t rule out future misuse, they decided to notify the customer. Notification.
And oh look, here’s yet another Experian breach where a client’s login credentials were misused to access their database. In this case, the client was Pitney Bowes and 2 Maryland residents were notified. The breach reportedly occurred between September 26 and November 21, raising questions as to why it took so long to flag.