“Because none of them seem to give a shit…”
– a hacker commenting on the lack of response to notifying the U. of Oklahoma that he had hacked them.
This blogger has repeatedly lamented the generally inadequate data security in the education sector and the fact that no federal agency actually enforces data security at the post-secondary level. Over the past few months, DataBreaches.net has posted numerous examples of universities that were attacked by SQLi attacks launched by Abdilo, Attorney, and Carbonic (among others). With a few notable exceptions, the universities either did not notice the attacks or did not acknowledge them publicly.
Even when hackers publicly alert institutions to their hacks on Twitter, the colleges and universities either do not seem to notice or respond.
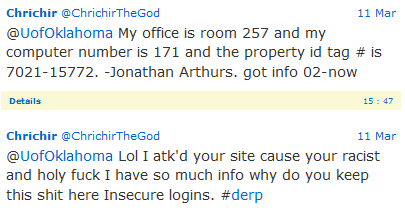
Last week, a self-proclaimed hacker tweeted to both the University of Oklahoma and South West TAFE in Australia that he had hacked them. While the tweets to U. of Oklahoma are no longer available, an archived copy of two of the tweets was made available to DataBreaches.net:
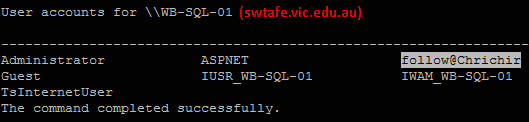
The tweet to South West TAFE is still available:
@swtafe nice users on your server pic.twitter.com/F1thWCw2fr
— Chrichir (@ChrichirTheGod) March 12, 2015
Neither the U. of Oklahoma nor SWTAFE responded to the hacker’s tweeted alerts of March 11. Nor have they (yet) responded to breach alerts sent to them last night by this site. Both hacks involved SQLi and the e-mailed breach alerts contained the vulnerable url used.
The hacker informs DataBreaches.net that because they did not respond to his tweets, he dumped their table structures in public pastes on March 12.
Given that the U. of Oklahoma has huge problems right now with the scandal over fraternity racism and free speech issues, ignoring the easy access to their databases when they should know that they are likely to be targeted by hacktivists is just… unwise. The tweets and the “University of Racism” reference in the paste should raise concerns that this might just be the beginning of more attacks to gain access to internal memos and/or student records.
In December, the U. of Oklahoma disclosed a breach involving its nursing college web server. What will it do now?
“Chrichir,” who claims to have operated alone in these attacks, informs DataBreaches.net that no personal information on students was downloaded, although “it would be easily possible to re-do” the hack. In a conversation with DataBreaches.net, he described his efforts to get U. of Oklahoma to respond:
And I told them I was able to access it, and then posted details from private posts to their office from 02-now and then no response …. I tweeted them because they had no response, ever. Then I released it [the paste] because STILL no care for their shit or that I was on their server. It’s like they don’t care about their security at all in the slightest?
I’m sure U. of Oklahoma would say that the security and privacy of student records is of their “utmost concern.” But does their lack of response betray any such claims?
So what will U. of Oklahoma (and SWTAFE) do now? And will it be enough to protect personal information held by U. of Oklahoma from angry hacktivists?