From MeetMeInYourCity.com, a site that describes itself as a “directory listing of independent escorts, exotic dancers, strippers’ adult entertainers, masseuse and escort agencies,” here’s part of their Terms & Conditions:
Secure technology is used to ensure your sensitive information is secure and protected from unauthorised access or improper use.
[…]
Your personal password is confidential and is encrypted to ensure its secrecy.
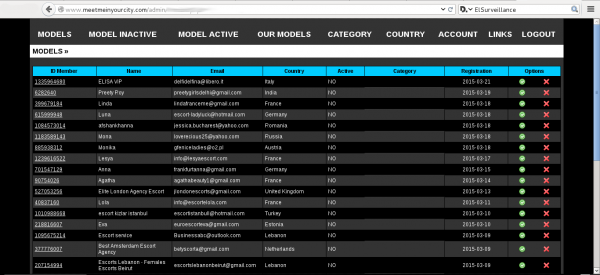
So why is there a data dump by @ElSurveillance of an alleged hack that shows 2,500 users’ email addresses with clear-text passwords?
DataBreaches.net sent an inquiry to MeetMeInYourCity.com last night to ask them to confirm or deny the data is from their database, and why, if it is their data, the passwords are in clear text. No response has been received as of this post, but this post will be updated if one is received.
MeetMeInYourCity is not the only escort-related site attacked by @ElSurveillance, whose profile says “An owl #Hacktivist – I aim to deliver a tiny message to the escort agencies, #EscortsOffline is their actual flag – I always use the front doors – #Dos.” See numerous instances of defacements on Zone-H. In the defacements, ElSurveillance leaves the following message:
Dear Admin and the clients
What such a great example you have given to the world
On how we can teach and raise our next generations
So they can live a much better life, Server and save our
Planet instead of just wasting their money and help
Spread the viruses just like every single stupid
Government in every single country do these days
Since you came all the way to here, They’re two things
That you can do while still viewing this page
1 – Turn on your volume and listen to the Qur’an & Just
Listening to your feelings instead of listening to the
Media and the stupid ISIS
2 – Have a look at your Logs which includes your IP
In the meantime, if you ever signed up for MeetMeInYourCity.com, you might want to change your password for that site and any other sites if you re-use passwords across sites.
Update: MeetMeInYourCity.com still has not responded to the notification and request for response, but @ElSurveillance provided the screencap below as proof of access to their server: