AS YOU WERE (UPDATE 3): Maybe we shouldn’t believe AshleyMadison’s denials. Despite AshleyMadison’s statement to Brian Krebs last night, a number of professionals who have been looking into the data dump believe it is authentic. The Guardian was able to verify the details on one of their journalists who had signed up for the site as part of their investigative reporting, and others have also reported verifying some of the data. According to the Guardian:
“I’ve now spoken with three vouched sources who all have reported finding their information and last four digits of their credit card numbers in the leaked database,” said Brian Krebs, who broke the news of the original hack.
Rob Graham, researcher from Errata security, said he was still analysing the leaked data but agreed that “it appears legit. I asked my Twitter followers for those who had created accounts. I have verified multiple users of the site, one of which was a throwaway account used only on the site. Assuming my followers aren’t lying, this means the dump is confirmed.”
STOP PRESSES (UPDATE 2): Brian Krebs interviewed AshleyMadison’s CTO who says the data dump does not appear to be genuine.
Original article follows:
As they threatened to do, Impact Team has seemingly dumped the data from AshleyMadison.com. The data dump is 9.6 GB, and preliminary impressions by a number of people who have started to inspect it suggest that this is really the data.
Keep in mind, however, that there’s no way of knowing whether names or email addresses included in the data dump are accurate, as the site does not verify personal information.
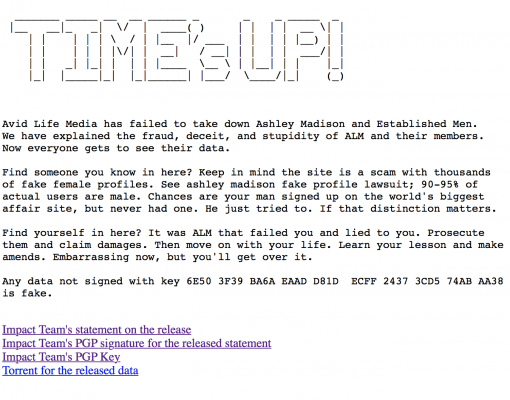
Time’s Up!
Avid Life Media has failed to take down Ashley Madison and Established Men.
We have explained the fraud, deceit, and stupidity of ALM and their members.
Now everyone gets to see their data.
Find someone you know in here? Keep in mind the site is a scam with thousands of fake female profiles. See ashley madison fake profile lawsuit; 90-95% of actual users are male. Chances are your man signed up on the world’s biggest affair site, but never had one. He just tried to. If that distinction matters.
Find yourself in here? It was ALM that failed you and lied to you. Prosecute them and claim damages. Then move on with your life. Learn your lesson and make amends. Embarrassing now, but you’ll get over it.
Any data not signed with key 6E50 3F39 BA6A EAAD D81D ECFF 2437 3CD5 74AB AA38 is fake.
Impact Team’s statement on the release
Impact Team’s PGP signature for the released statement
Impact Team’s PGP Key
Torrent for the released data
[Links removed by DataBreaches.net]
DataBreaches.net will have more on this after there’s been more analyses of the data.
Update 1: Some preliminary numbers and description of files from Hydraze & Friends.
Note: The headline of this entry has been changed post-publication.