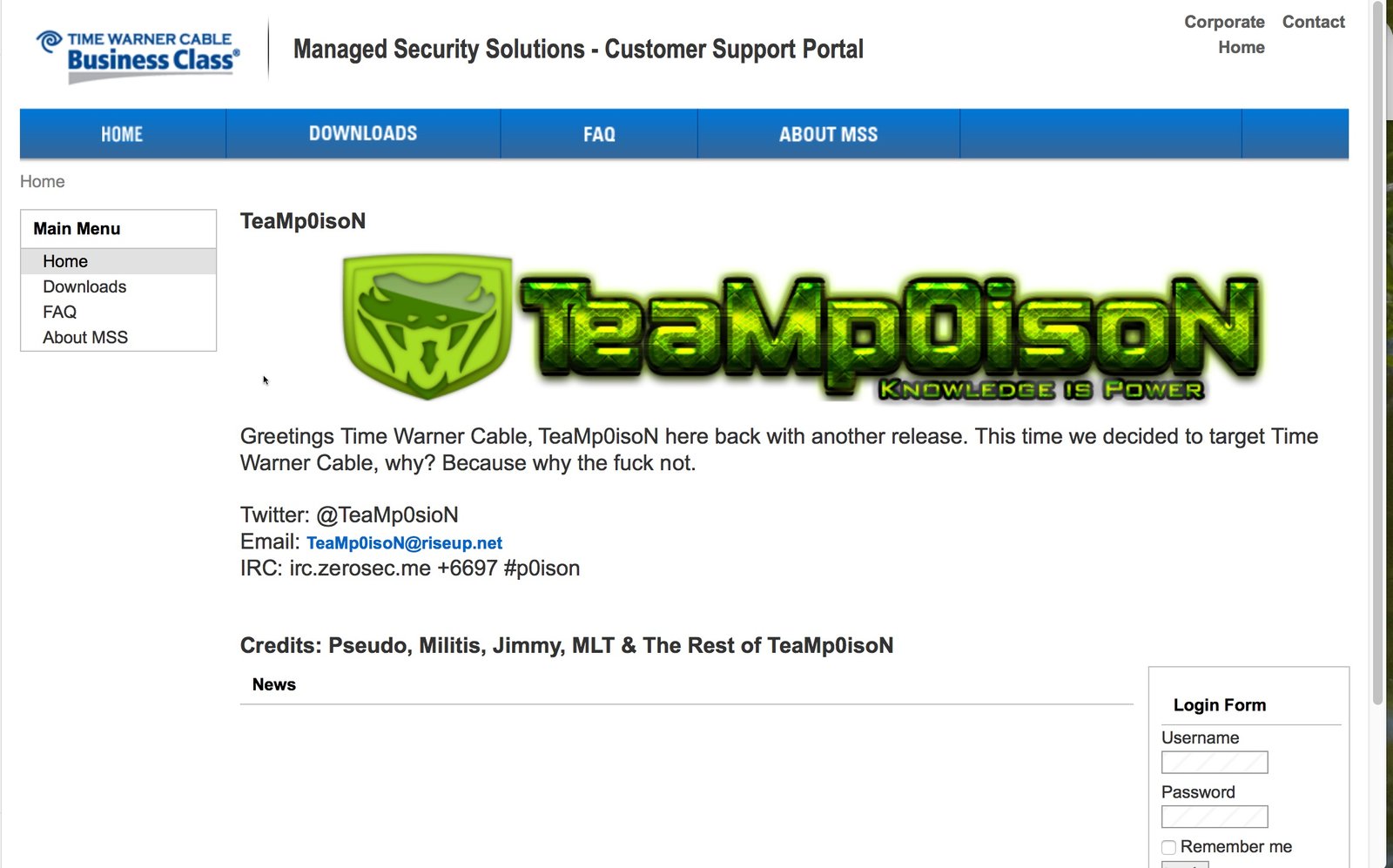
It looks like TeaMp0isoN’s been busy again. This time it’s the Time Warner Cable Business Class Managed Security Solutions portal that got hacked with the following defacement left as a message:
The @TeaMp0sioN Twitter account announced the breach by Pseudo, Militis, Jimmy, and MLT on Sunday afternoon, followed shortly by a data dump consisting of 4,191 records containing IDs, usernames, email addresses, and encrypted passwords. Not all of the data appear genuine (i.e, there were some dummy accounts). The most recent entry in the dumped data appeared to be from the second half of January.
DataBreaches.net notified TWCBC’s technical support department of the breach by phone.
I’m going to go out on a limb and guess that this was an SQLi attack, but have asked TeaMp0isoN to confirm.
Update: They confirmed it was SQLi.
Update 2: The portal is now offline.