On March 15, Jessica Gavin reported:
A cyber security breach, striking Methodist Hospital in Henderson. We’re learning the FBI is investigating this right now, but there’s some good news.
[….]
David Park, COO of Methodist, tells 14 NEWS the hackers have copied patients records and locked those copies. They’ve deleted the originals.
“We’ve notified the FBI, we’re dealing with federal authorities on how to deal with it,” said David Park, Methodist Hospital COO. “Depending upon the number of records that were locked, depends upon whether we’re going to consider looking into whether we pay anything or not.”
In a release, hospital officials say they want to reassure patients their information is secure. They say, they activated a back-up system while the main network was locked down. The hospital has been able to run smoothly without interrupting daily operations.
As of today, the hospital tells local media that their system is “up and running,” but it’s not totally clear whether that means that they recovered access to the files or whether they are referring to the backup system that they activated. The hospital’s web site still displays an emergency alert:
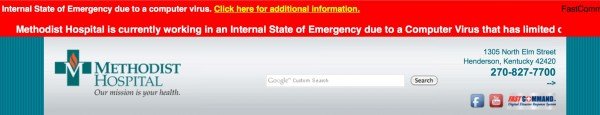
“Methodist Hospital is currently working in an Internal State of Emergency due to a Computer Virus that has limited our use of electronic web based services. We are currently working to resolve this issue, until then we will have limited access to web based services and electronic communications.”
So far, none of their media releases have indicated what type of ransomware this is and what the amount of the ransom demand is.
Update of Mar. 23: Brian Krebs reported yesterday that it is .Locky strain of ransomware and that the attackers demanded 4 btc.
Update: They reportedly did NOT pay any ransom.