Early today a hacker using the handle pravyy sector announced a leak of data from Central Ohio Urology and made claims that it was 156GB in total.
The dump of data appears to be a copy of a file system from software used in medical practices to help organize and share documents around the local and external networks. The software, DocPlus, which claims to of started in 1989 and is by doctors for doctors makes claims to interface with many other medical based software to help share their documents and information.
After doing some quick checks of the data i have also discovered that a vast majority of it is related to internal documentation, with templates of documents used for employment, auditing, tracking of information and other internal stuff.
Facts
- 46,670 doc(x)
- 54,578 pdf
- 1,526 zip
- 158,359 xls(x)
- 521,659 total files, which include exe, images and other random extensions related to software used by Ohio Urology
- File dates range from early morning 21st July to late night 22nd July
- Reports of patient visits to the officers with full detailed descriptions of what happened, what the doctor did and the outcome and diagnosis if any.
- Scans of documents with patient details
- Documents with patient details, names, addresses, dates of births, medical information, partial social security numbers
- Lists of "re-calls" which are used to remind patient’s that they ave not visited the clinic for some time or have a upcoming scheduled appointment
- NextGen Patient records
- Patient Withdrawal from Care Letters, telling them that they can no longer visit any of the 27 locations for care from Ohio Urology
- software from the IT department – including serial numbers in .txt files!
Ransomware
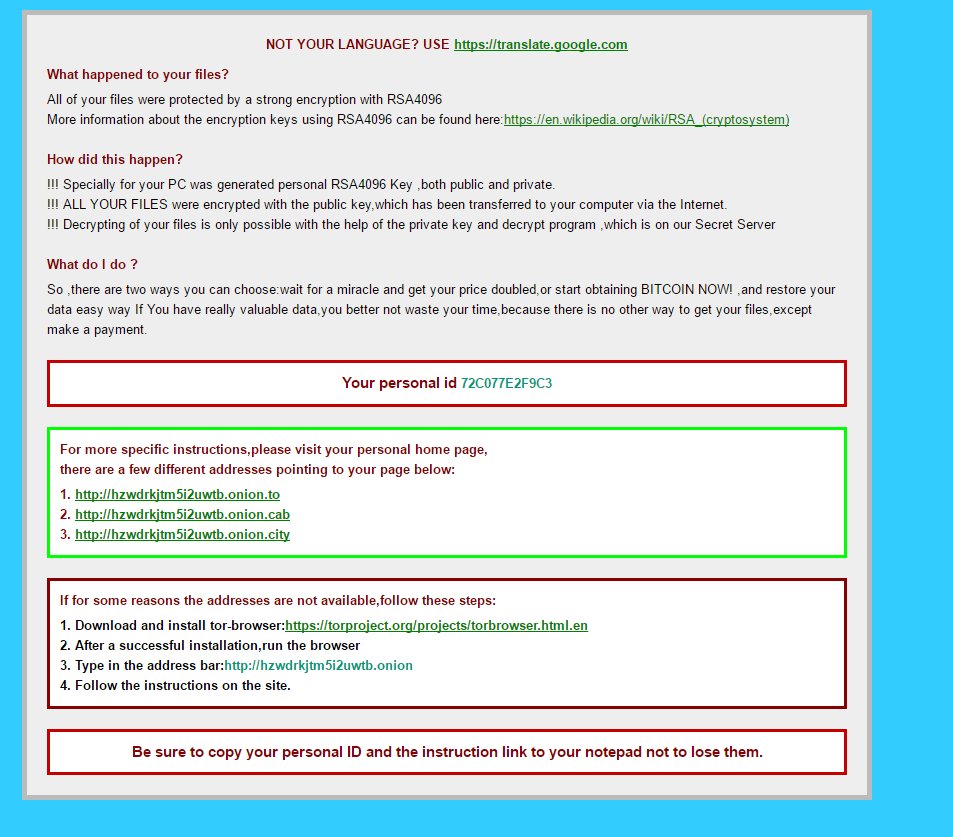
While researching this data i had come across a html file that got my eye, with a name like !1Recovery_72C077E2F9C3.html it was pretty clear that this was not normal and after checking it, it appears that it this is a ransomware lock page.
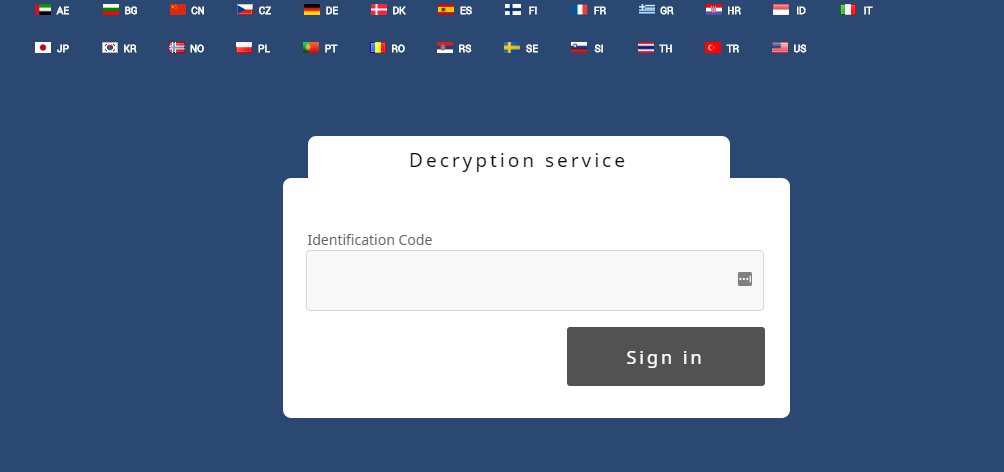
The page was very basic and when checking the link to the decryption service it appeared to be online still.
Could this be the cause to this leak coming out? Has Ohio Urology become yet another victim to ransomware?
Looking into the ransomware gives a decent insight to when the systems got breached, after doing some research and asking around a bit it was pretty easy to point the finger at cryptxx 1.0, which was mostly seen out in the wild starting about 4 months about and lasting 2 months after that.
The lock screen is identical to the this one here https://www.proofpoint.com/us/threat-insight/post/cryptxxx-new-ransomware-actors-behind-reveton-dropping-angler and version 2.0 of this variant of ransomware had a known change of design on the lock page, that is not to say there was not old copies or other people using this still once new versions have come out.
The files that are effected by this seem to be located to one directory which belongs to the Olentangy Location for Ohio Urology, they appear to be in a archived format which suggests to me that this incident has been "solved" or the infected system was restored and a copy of the infected system has been made and stored and as a result of this breach its now leaked to.
So it really confirms that staff at Ohio urology have been targeted for some time and possibly not by just one person. there appears to be no media reports or no reports in general from Ohio urology about this incident which is also a worry, did the ransomware infect and breach client credentials to? if so and they knew about it, why have they not put out breach notification.
Crypto file facts!
- 10784 .crypt files
- 1548 instances of !Recovery_72C077E2F9C3.html
- can only be found in the Olentangy directory.
Effected Centers
Other centers would may be effected as well but so far it seems mostly it is those listed above.
Some other coverage so far:
by Motherboard
by Databreaches.net
By Zack Whittaker