From the U.S.A.O. press release:
OAKLAND – A federal grand jury in Oakland indicted Yevgeniy Aleksandrovich Nikulin yesterday for obtaining information from computers, causing damage to computers, trafficking in access devices, aggravated identity theft, and conspiracy, announced United States Attorney Brian J. Stretch and Federal Bureau of Investigation Special Agent in Charge John F. Bennett.
The indictment, unsealed today, alleges that Nikulin, 29, of Moscow, Russia, accessed computers belonging to LinkedIn, Dropbox, and Formspring, each of which has its headquarters in the San Francisco Bay Area. The indictment further alleges that the defendant accessed the computers without authorization and that he obtained information from the computers. According to the indictment, the defendant also caused damage to computers belonging to a LinkedIn employee and to Formspring by transmitting a program, information, code, or command. Nikulin also is alleged to have used the credentials of LinkedIn and Formspring employees in connection with the computer intrusions. Further, Nikulin is alleged to have engaged in a conspiracy with unnamed co-conspirators to traffic stolen Formspring user credentials. In all, Nikulin is charged with three counts of computer intrusion, in violation of 18 U.S.C. § 1030(a)(2)(C); two counts of intentional transmission of information, code, or command causing damage to a protected computer, in violation of 18 U.S.C. § 1030(a)(5)(A); two counts of aggravated identity theft, in violation of 18 U.S.C. § 1028A(a)(1); one count of trafficking in unauthorized access devices, in violation of 18 U.S.C. § 1029(a)(2); and one count of conspiracy, in violation of 18 U.S.C. § 371.
Defendant was arrested on October 5, 2016, by officials in the Czech Republic pursuant to a provisional arrest request based on the warrant issued in connection with the complaint. He remains in custody in Prague.
An indictment merely alleges that crimes have been committed, and all defendants are presumed innocent until proven guilty beyond a reasonable doubt. If convicted, the defendant faces the following maximum penalties:
- 18 U.S.C. § 371: Five years of imprisonment, $250,000 fine (or alternatively, twice the gross gain or gross loss, whichever is greater), three years of supervised release, $100 special assessment, forfeiture, and restitution.
- 18 U.S.C. § 1028A(a)(1): Two-year mandatory minimum sentence of imprisonment to run consecutive to any other sentence and in addition to the sentence for the underlying felony, $250,000 fine (or alternatively, twice the gross gain or gross loss, whichever is greater), three years of supervised release, $100 special assessment, restitution.
- 18 U.S.C. § 1029(a)(2) and (c)(1)(A)(i): Ten years of imprisonment, $250,000 fine (or alternatively, twice the gross gain or gross loss, whichever is greater), three of years supervised release, $100 special assessment, forfeiture, and restitution.
- 18 U.S.C. § 1030(a)(2)(C) and (c)(2)(B): Five years of imprisonment, $250,000 fine (or alternatively, twice the gross gain or gross loss, whichever is greater), three years of supervised release, $100 special assessment, forfeiture, and restitution.
- 18 U.S.C. § 1030(a)(5)(A) and (c)(4)(B)(i): Ten years of imprisonment, $250,000 fine (or alternatively, twice the gross gain or gross loss, whichever is greater), three years of supervised release, $100 special assessment, forfeiture, and restitution.
However, any sentence following conviction would be imposed by the court after consideration of the U.S. Sentencing Guidelines and the federal statute governing the imposition of a sentence, 18 U.S.C. § 3553.
Michelle J. Kane is the Assistant U.S. Attorney who is prosecuting the case with the assistance of Melissa Dorton and Elise Etter. The prosecution is the result of an investigation by the Federal Bureau of Investigation with the assistance of authorities in the Czech Republic and the U.S. Department of Justice’s Criminal Division, Office of International Affairs.
Further Information:
Case #: CR 16-00440 WHA, 16-71303 MAG
# # #
Related: Indictment
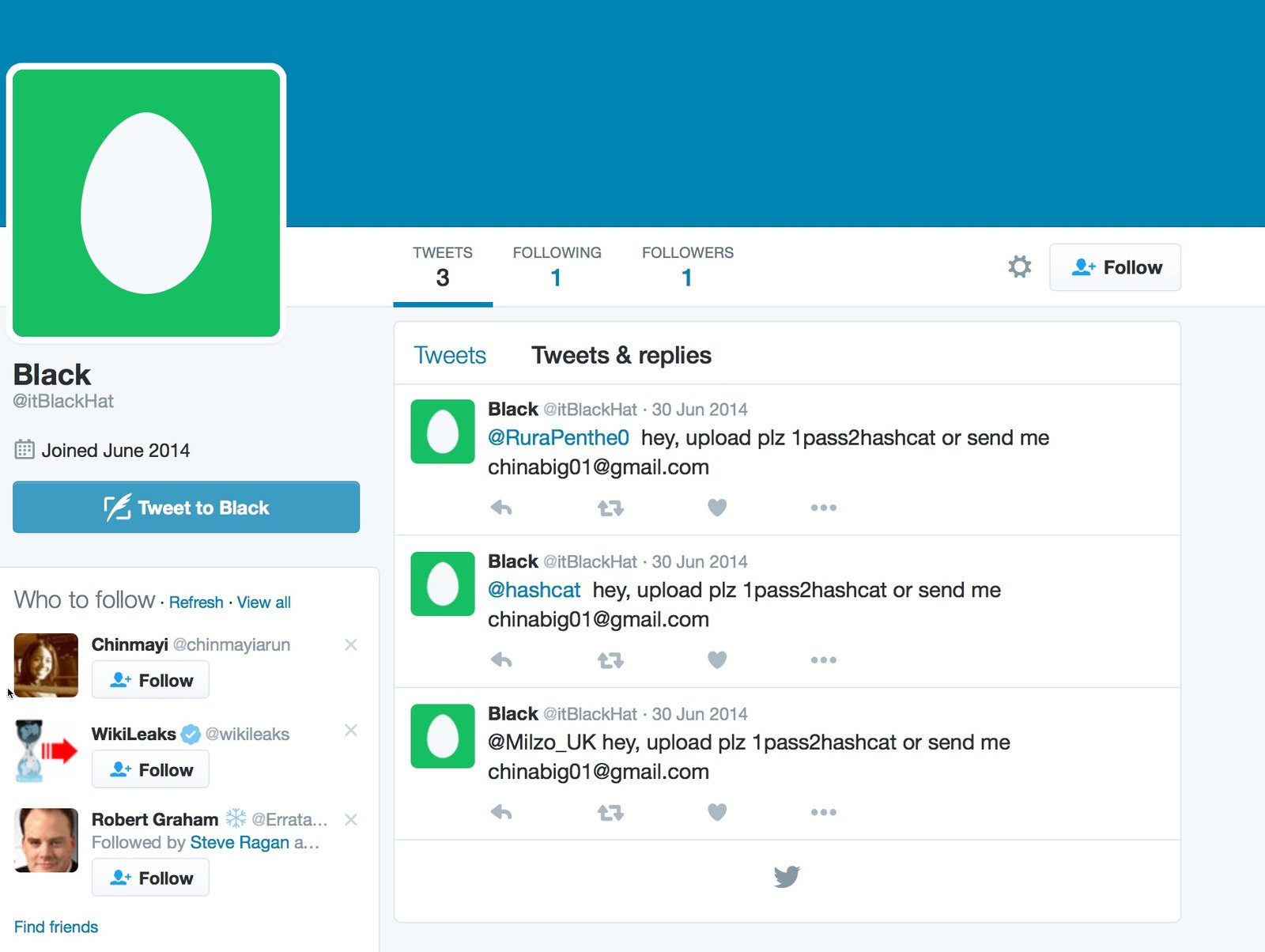
N.B. Nikulin’s online screen names were allegedly ChinaBig01, dex.007, valeriy.krutov3, and itBlackhat.