As regular readers know by now, DataBreaches.net has been compiling reported instances of W-2 phishing scams. As part of that investigation, I decided to take a quick look today at some dark net marketplaces to see if any data were up for sale. Brian Krebs had reported on this issue in January after finding a dedicated marketplace. I decided to check some others.
Within minutes, I found listings for 2016 W-2 data, although it is not clear from the listings where the data are from or how they were obtained. Here are some of the listings:

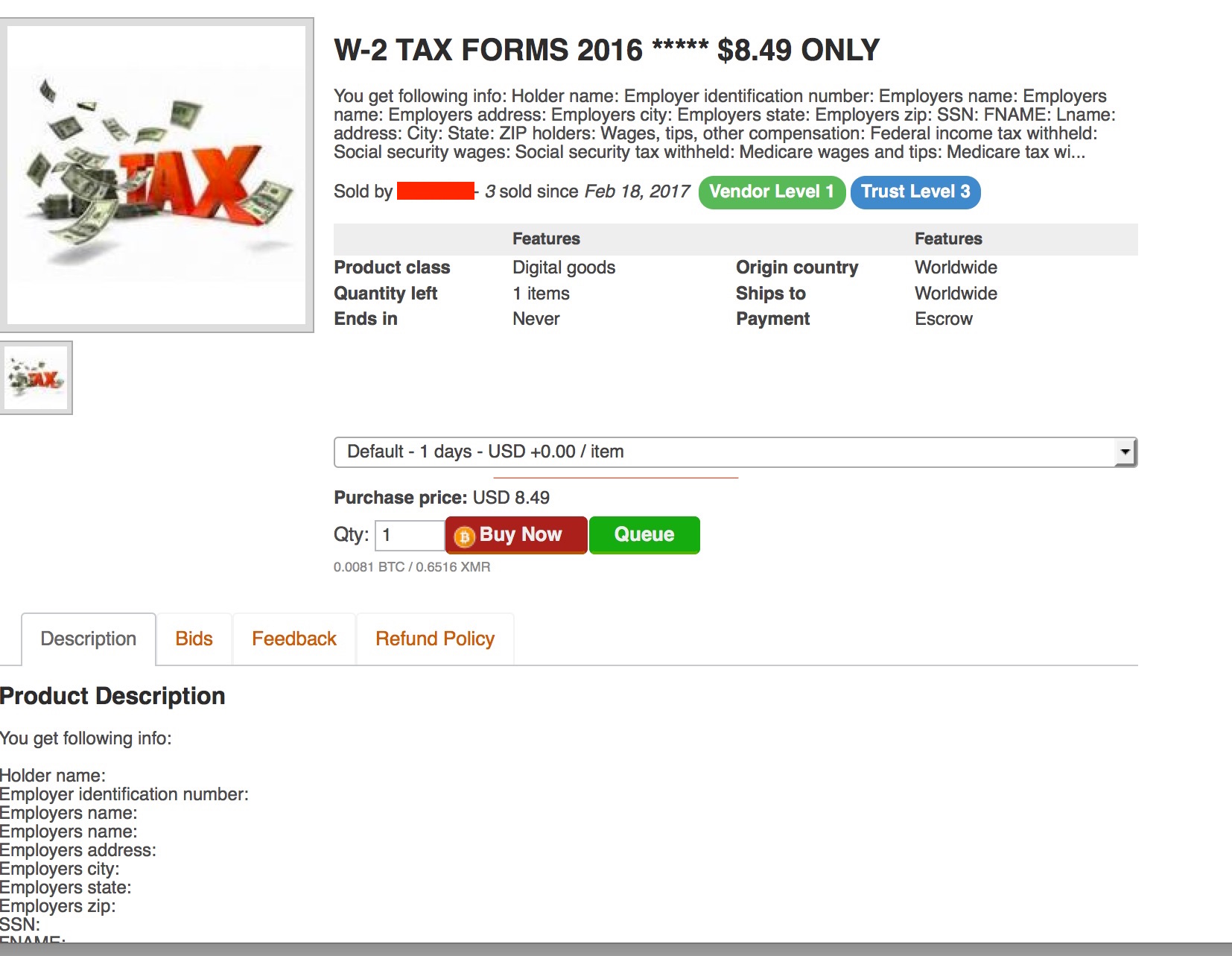
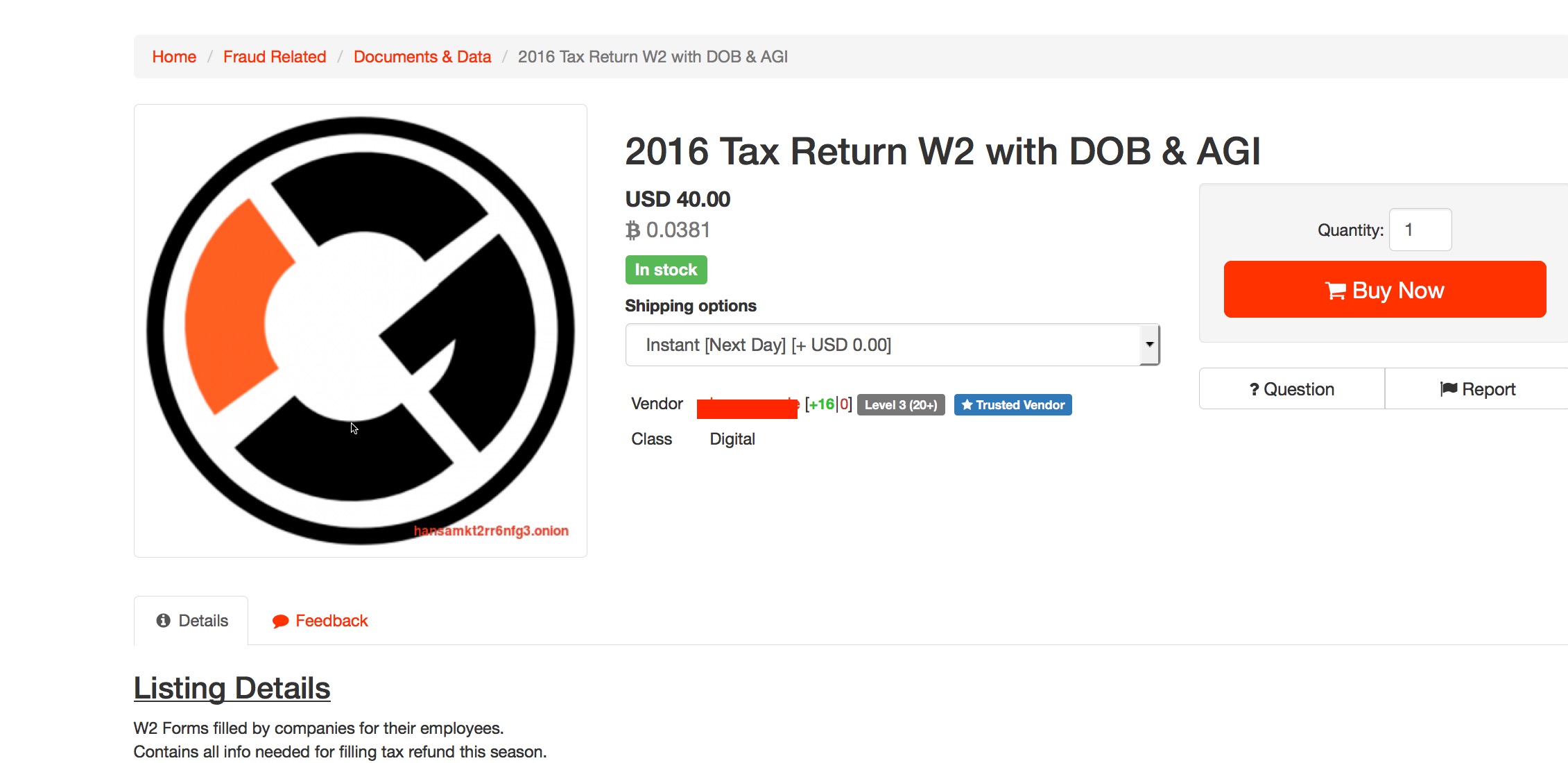
DataBreaches.net attempted to find out whether the data in the first two listings might be from any of the known W-2 incidents. One vendor responded that most of the ones for sale are from Florida, while the rest are from Hawaii, North Carolina, South Carolina, and California. DataBreaches.net has reported on phishing incidents in schools in most of those states already, and is trying to obtain additional details from the vendor. The second vendor stated that all of his listings are from just one state, and I’m trying to find out which one. I’ve asked both vendors whether they’ll tell me if any are schools.
The third listing linked to a sample with an unredacted W-2 form. The employer was not a firm that has reported having any breach this year, and an attempt to contact the employer was unsuccessful as the phone number obtained in a Google search has been disconnected.
Similarly, DataBreaches.net found another listing that is not being posted on this site just yet because the sample image came from a college in Florida that has not disclosed any W-2 incident this year. DataBreaches.net called the college and left a detailed message with their campus security about the concern and offered to send them the information on the marketplace listing and the partial employee information that was visible in the listing. Although some of the information in the sample W-2 was redacted, DataBreaches.net was able to track down the employee whose W-2 this would be. The employee confirmed that the data were his data but because he admitted having a copy of his W-2 on his personal device, it’s still not clear whether there was a compromise at the college or a compromise of just the individual employee.
This post will be updated if more information becomes available.
Update 1: The vendor who indicated that all W-2’s were from one state indicated that the state was Florida, and that the source was companies (not schools).
Update 2, Feb. 20: The employee of the Florida college that I’m not naming at this time contacted me to say that he had checked and there was no copy of the W-2 on his personal devices. This morning, I spoke with the CIO of the college who had called me in response to my message yesterday, and they will be investigating. This post will be updated once they complete their investigation and let me know whether it appears that they have had a breach or not.
Update 3, March 6: See more about the college’s breach in this post.