Back in January, this site reported that Grey Eagle Resort & Casino in Calgary had been hacked and some personal employee data had been dumped. At the time, the hackers threatened to dump more data.
 The casino never responded to multiple inquiries from this site about the breach, but did confirm it to Global News. No explanation was ever offered publicly by the hacker(s) to explain their motives.
The casino never responded to multiple inquiries from this site about the breach, but did confirm it to Global News. No explanation was ever offered publicly by the hacker(s) to explain their motives.
Last night, DataBreaches.net received an email from the same individual who pointed us to the January data dump. This time, the correspondent wrote:
looks like grey eagle casino down played the hack on their casino.
more data has been dumped I came across this on pastebin
The paste was terse:
Grey Eagle Casino has been owned.
our group has hacked Grey Eagle Casino. Employee, Customer and corporate information has been taken.
The hackers, who do not provide any name for themselves, linked to a password-protected data dump on Mega.nz, and indicated that the data would also be uploaded to torrent sites “soon,” with more data dumps to follow in the coming weeks.
The data dump contained 1.7 GB of mainly employee and corporate files.
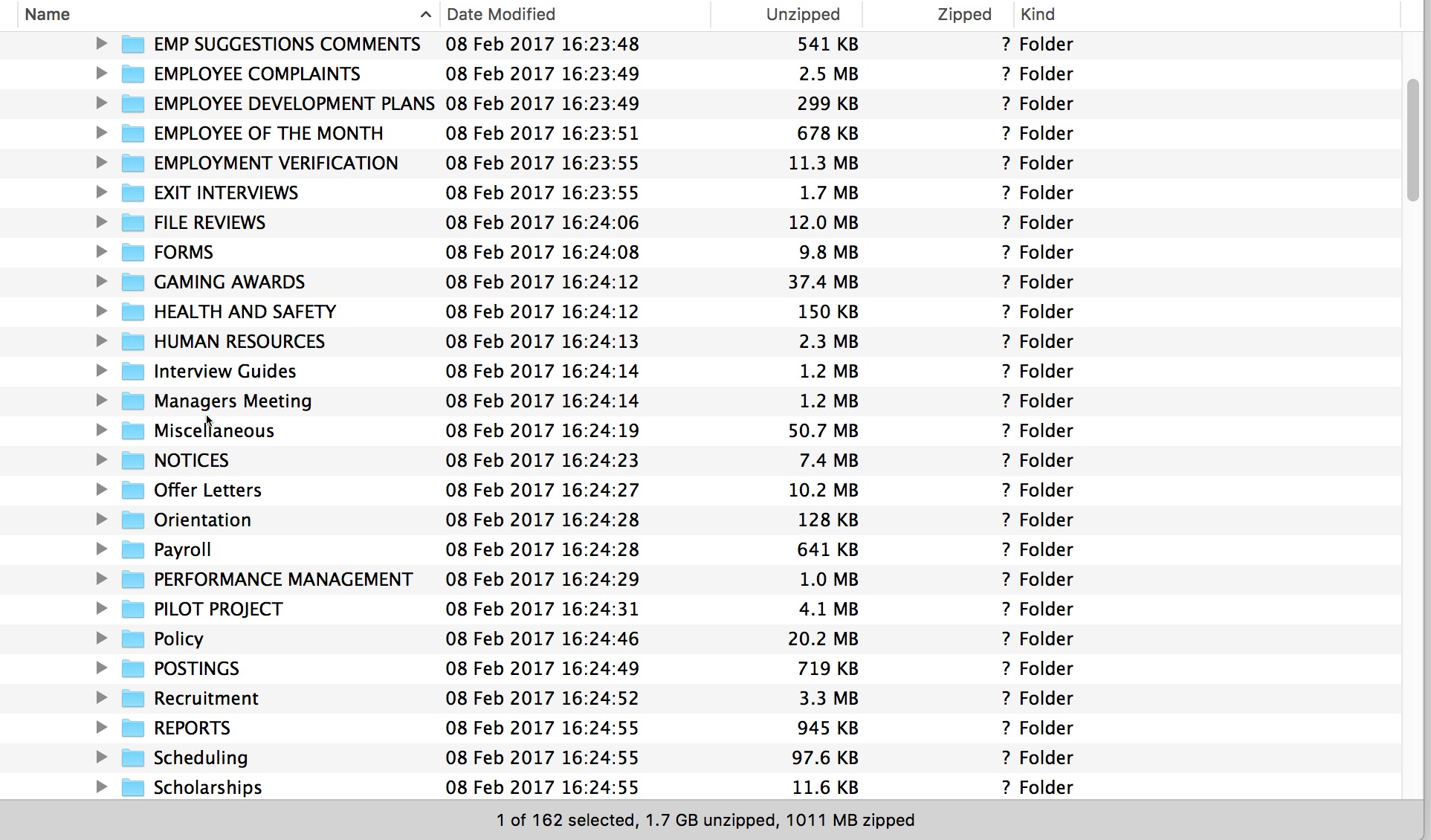
The files contain a great amount of employee information such as names, addresses, positions, salary information, disciplinary issues, medical leave reasons, and termination letters. Inspection of the data dump also reveals that the files appear to have all been created before the first January dump, with just new time-stamps for the directories. So the hackers likely acquired all this data before their first release and are just releasing it now.
But once again, the hackers offer no explanation as to why they are targeting Grey Eagle Resort & Casino and showing no regard for its employees. And once again, the casino hasn’t answered any questions posed by this site.
Why wait more than 3 months for another data dump? Are these hackers doing what TheDarkOverlord has done at times – dumping data and seeking media coverage to put an intended victim under more pressure to pay up? Maybe the hackers will decide to share more about their motives. Or maybe Grey Eagle will decide to be forthright about what’s going on. I guess we’ll just have to wait and see.
They are acting alot like how TDO is. Did you see tampabay surgery center on they’re twitter?
I’m not understanding the second part of your comment. Did I see TampaBay Surgery on whose Twitter? TDO’s? Yes, I blogged about it here: https://www.databreaches.net/thedarkoverlord-dumps-180000-patients-records-from-3-hacks/