Protenus has published its Breach Barometer for April, with data and some analyses provided by this site. The analyses were based on the following incidents:
- Amedisys Home Health
- Area Agency of Aging 1-B: On March 31, 2017 the Area Agency on Aging 1-B (AAA 1-B) became aware of an unintentional potential disclosure of the personal health information (PHI) of 1741 program participants. Two separate unencrypted emails containing the participant’s name, case number, claim payment amount, units of service, service codes and vendor code of AAA 1-B participants were sent by the AAA 1-B to the Michigan Department of Health and Human Services (MDHHS) Aging & Adult Services Agency on March 23 and March 30.
- Ashland Women’s Health
- Atlantic Digestive Specialists
- Behavioral Health Center
- BioReference Laboratories, Inc.
- Cardiology Center of Acadiana
- Carson Valley Medical Center: Following the receipt of a fake email, a CVMC employee released a single spreadsheet that included patient first and last names, patient account number, service discharge date, and identification of the location of treatment as CVMC.
- Central New York Psychiatric Center
- Cleveland Metropolitan School District
- CVS
- Erie County Medical Center
- Eyecare Services Partners Management, LLC
- GlaxoSmithKline Patient Assistance Program
- Greenway Health
- Harrisburg Endoscopy and Surgery Center, Inc.
- Harrisburg Gastroenterology
- Hill Country Memorial Hospital
- Humana Inc [case # HU17001CC]
- Iowa Veterans Home
- LifeSpan
- Memorial Healthcare
- Memorial Hospital Clinic South
- Memorial Hospital Clinic West
- Michigan Facial Aesthetic Surgeons d/b/a University Physician Group
- MVP Health Care, Inc.
- Pentucket Medical
- Spine Specialist
- St. Lucie County
- University of Oklahoma, OU Physicians
- University of South Florida
- Valley Women’s Health, S.C.
- Virginia Mason Memorial
- Western Health Screening
Significantly, perhaps, one of the worst incidents in terms of potential harm to individual patients was one that only appeared on HHS’s breach tool because this site discovered it and notified the entity that its patients’ psychotherapy records appeared to be up for sale on the dark web.
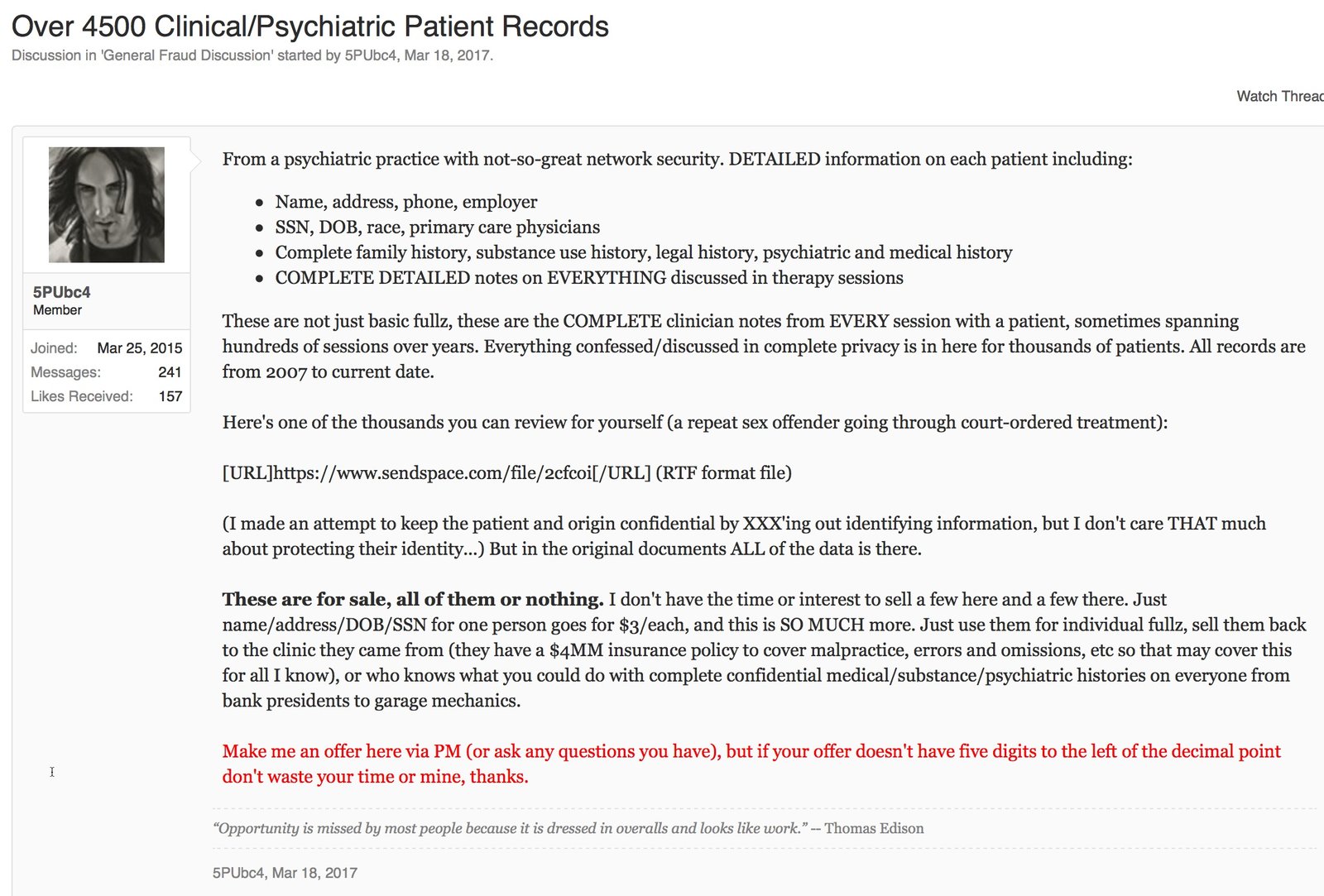
Of note, the hacker never attempted to extort the clinic to see if the clinic would pay to get the data back – the data were just put up for sale with an asking price of a minimum of $10,000.00 (about $2-$3 per patient).
Another candidate for worst breach of the month was the Erie County Medical Center ransomware attack, which is still not totally resolved. Thankfully, the center had backups and other means of accessing patient records and information or the impact on care could have been a nightmare.
While DataBreaches.net considered these perhaps the worst breaches of the month (admittedly a somewhat subjective determination), perhaps my biggest concern in reviewing the April data was wondering how many incident reports we are not seeing on HHS’s breach tool. Are we missing so many incidents from both HIPAA-covered and non-HIPAA-covered entities that what we do know about is not really representative of what’s going on with threats to health data security? Is HHS’s public breach tool giving us any kind of accurate insights into risks and breaches involving health data, or is it just significantly underestimating and misrepresenting the real risks? I’ll have more to say on this in another post.