More entities are falling prey to SamSam ransomware. Hannah Grover reports:
The city of Farmington is returning to normal after a variant of the ransomware known as SamSam shut down the computer systems.
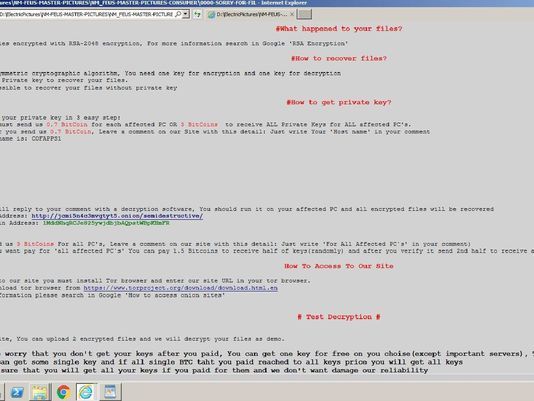
The virus encrypts files on a computer network or locks down the entire system. When people attempt to log on, they receive a message informing them that the files have been hijacked and they will have to pay to get them back.
City Manager Rob Mayes said via text message that the FBI advised the city not to pay the 3 bitcoin — worth more than $35,000 — ransom that was demanded. Mayes said the city was able to recover the encrypted information without paying ransom.
Many of the business operations computers were encrypted on Jan. 3 by a variance of the SamSam ransomware.
Read more on Daily Times, who were able to obtain a copy of the ransom message, reproduced below:
The city’s press release of January 17, informed the community, but does not seem to disclose how the malware got into the system. Was this another phishing situation? They may not have been able to answer that question yet:
Farmington, NM: The City of Farmington continues to work with the FBI and other outside services to investigate the cause and originating location of the ransom ware that encrypted many business operations computers on January 3, 2018. Information Technology (IT) personnel have been able to confirm that the City was attacked by a variance of the SAMSAM ransom ware.
The City apologizes for the temporary inconvenience our customers may have experienced during this time. Nearly all business systems related to customer service operations have been restored.
While the FBI has confirmed that attacks like this are happening all over the world on a daily basis, the City would like to emphasize:
- No City customer or employee personal information was extracted
- The City’s public administration system was not affected
- There was no breach of any electric utility operations systems
- There was no interruption of any public safety services
- City email systems were not affected and are safe
The City of Farmington invests significant resources in the latest technology in virus defense, including specific ransom ware software and multiple levels of virus protection. The City has enlisted additional outside resources to review security protocols and make recommendations regarding any improvements that may be implemented.
via @CampusCodi, who provides additional details on the profit the criminals seem to be reaping since December.
Update: The Allscripts incident has also now been confirmed to have involved SamSam, and as also covered previously on this blog, we know that the Hancock Regional Hospital and Adams Memorial Hospital incidents also involved SamSam.