In July, 2013, H-E Parts International, a manufacturer of aftermarket parts and components for the mining industry, acquired The Morgan Group. Morgan already had an established reputation for servicing the mining, oil, and gas industries.
 Together, H-E Parts International Morgan grew as a global corporation with offices in Canada, Chile, Australia, China, Peru, and throughout the United States.
Together, H-E Parts International Morgan grew as a global corporation with offices in Canada, Chile, Australia, China, Peru, and throughout the United States.
Unfortunately for them, however, they appear to have become a multinational victim of the criminal hackers known as TheDarkOverlord (TDO). In an encrypted chat with this site, a spokesperson for TDO claimed that they had obtained all of H-E Part Morgan’s files – “everything.”
[DataBreaches.net refers to TDO in the plural as it appears there is more than one person involved, and TDO claims to be more than one person.]
DataBreaches.net does not know exactly when H-E Parts Morgan first became aware that they had been hacked, but the hack appears to have occurred – at least in part – in November.
As of today, however, DataBreaches.net has found no indication that there has been any public disclosure of the breach or notification to those affected. Two of the states in which the firm has offices – Montana and Washington – make breach reports submitted to the state publicly available on their websites, but there is currently no notification from H-E Parts Morgan on either site. Does the firm have any employees in those states? It would seem likely that they do, but have the employees been notified that TDO acquired their personal information? If not, will they be notified? Or does H-E Parts Morgan dispute TDO’s claim that they acquired personnel information on U.S. employees?
H-E Parts Morgan did not respond to multiple inquiries from this site.
When asked whether H-E Parts Morgan definitely knew that they had been hacked, and whether they had actually responded to any contacts or extortion demands by TDO, a spokesperson for TDO reported that the firm definitely knew, and that one executive had responded to them, “Fuck you.”
As more objective proof of the hack, DataBreaches.net was provided a 1.4 GB sample of documents exfiltrated by TDO in November. The screenshot below shows the directory and filenames of just some of the files:
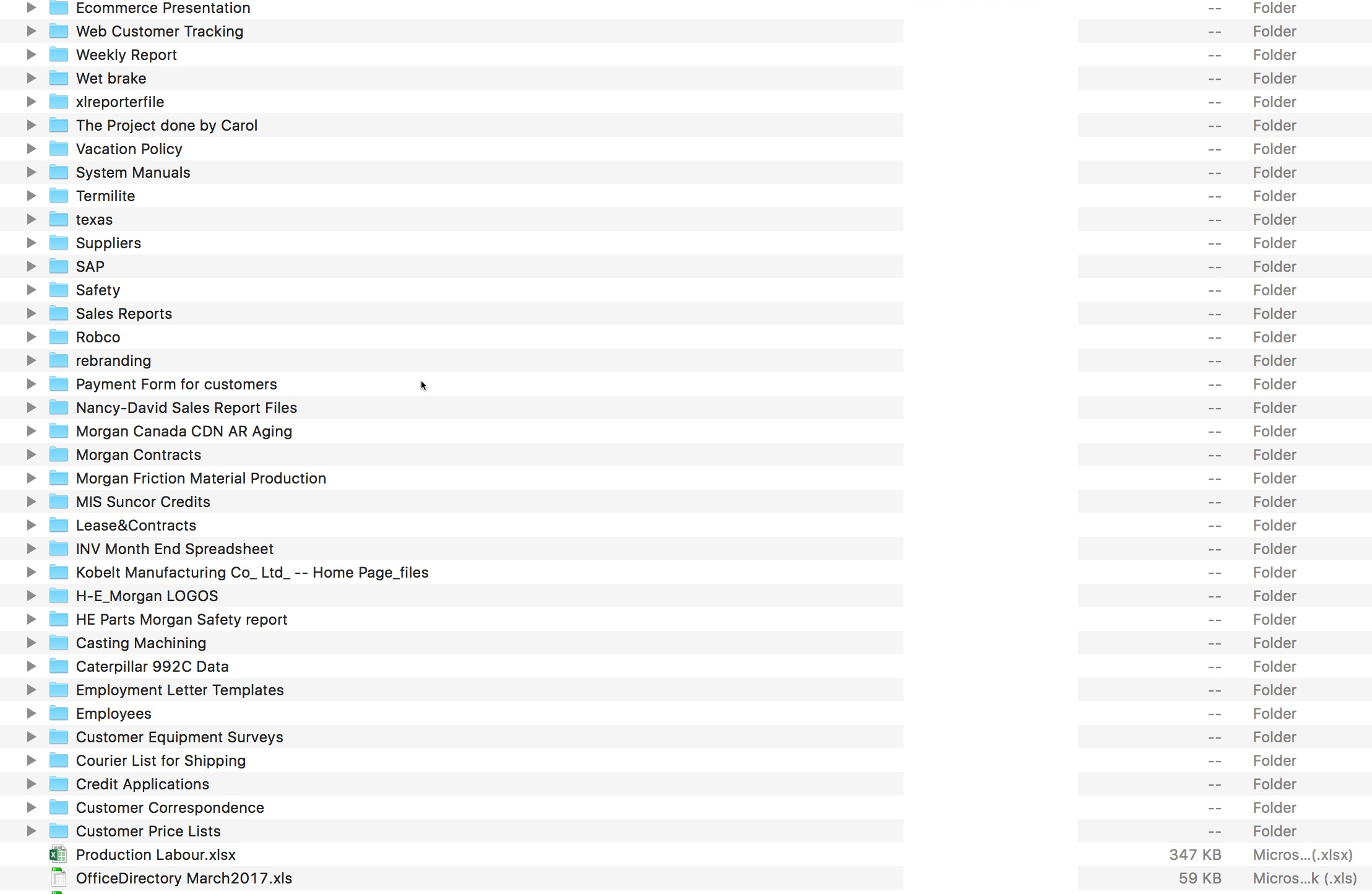
Some of the files were password-protected, such as a file containing emergency contact information. Other files contained records of orders and other business operations and finances.
I suspect regular readers of this site realize that the mining industry is not one of my personal priorities or interests. I do not know how large the extortion demand was that H-E Parts Morgan allegedly refused to pay, but once again I found myself wondering about the similarity between TDO’s methods and those of a group of hackers that Mandiant has called FIN10. And I wish I could offer readers some brilliant insight or definite answer as to whether there is a relationship between the two entities, but alas, I can’t. Once again, I have questions but no answers.
But the bottom line of this particular post is that H-E Parts Morgan was hacked and so far, there does not appear to have been any public disclosure or notice of that. If employees weren’t notified, were any clients notified, or did the firm assess risk and decide that no client notification was required? And apart from any notification requirements in the U.S., does this claimed hack trigger any notification or disclosure requirements in Canada or the other countries where they have a presence?
TDO’s spokesperson offered no clue as to what, if anything, the hackers might do with the data they exfiltrated.