On February 6, this site broke the news that some data from the CarePartners hack of 2018 was being dumped publicly, presumably as a way to increase pressure on CarePartners to pay the “requested” fee for the hackers not to release any more data.

As noted in the February 6 report, there were two data dumps. The first one, allegedly containing financial and employee information, did not download correctly and this site was not able to actually get the files and examine them at that time. The second dump, allegedly containing more than 80,000 patient medical files, did download completely, but that dump is encrypted and the hackers will only provide the encryption key to anyone willing to pay 5 BTC for the key.
In response to my request for them to provide a working link for the first data dump, “Team Orangeworm” provided this site with another link to the 891 MB data dump. When extracted, the archive was 2.2 GB and contained 12,971 files in two folders, “FINANCE,” and “Scotia Reports.”
Because CarePartners declined to answer my questions but had indicated that they had not been able to verify the hackers’ claims in 2018, I am including a partial screenshot of the contents of the FINANCE folder:


Data in the dump was not current data for June 2018, but the files provided do support the hackers’ claims that the dump contained:
Company Financial documents
Hundreds of employee T4 statements (with SINS,DOB,Name,Address)
company banking information, accounts payable and wire transfers
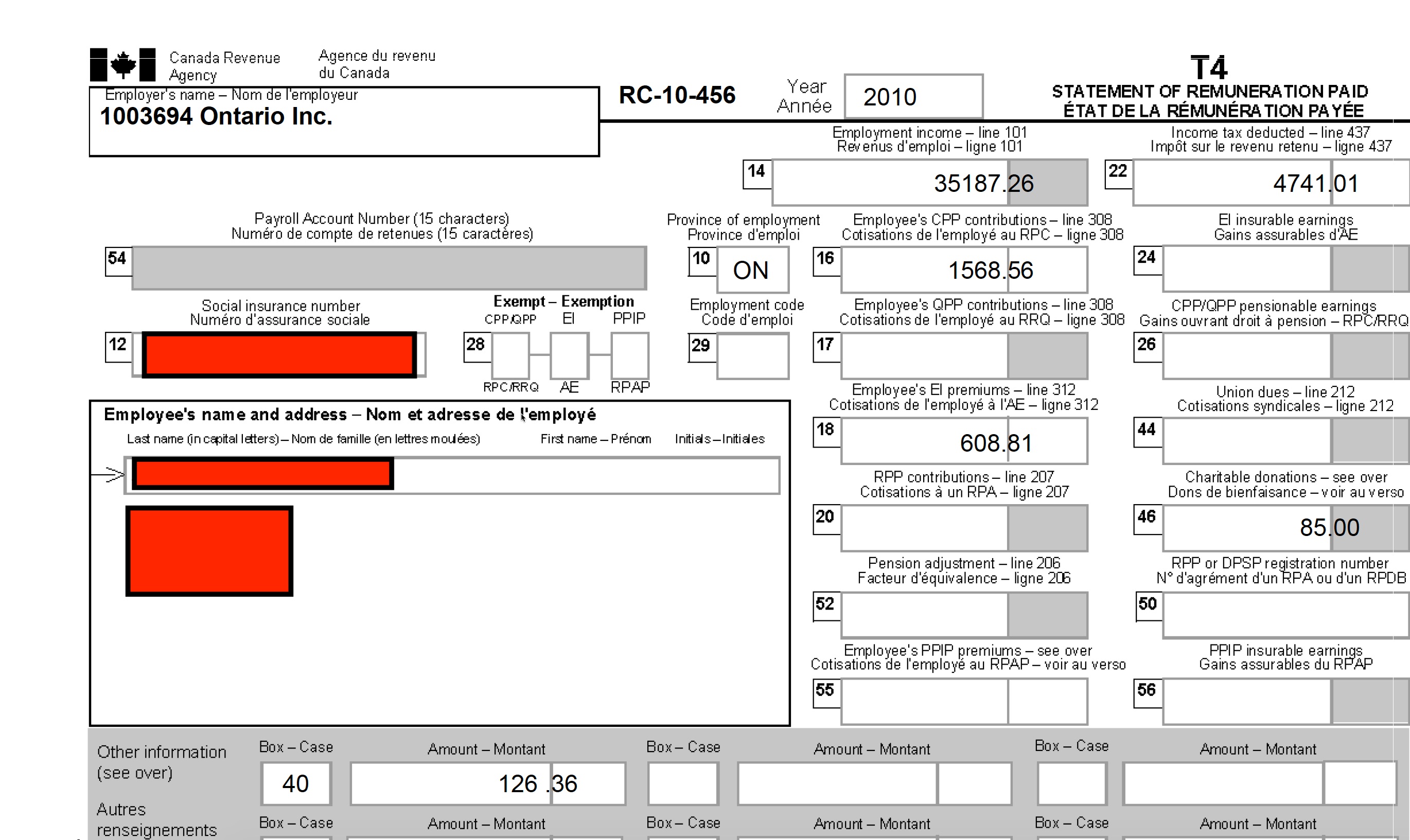
As one example, the 2010 T4 (Employee Copy).pdf file contains 724 T-4 forms where each form includes the employee’s name, address, social insurance number, and wage and deductions information. One form from that file, redacted by DataBreaches.net, appears below for illustrative purposes:
The hackers claim that they have three other dumps with employee and corporate files that they will release at some point. Perhaps those files contain more current financial and employee data.
The patient data, however, are allegedly in the second dump that requires an encryption key that the hackers are trying to sell for 5 BTC.
To be clear on one point because I did not address this directly in my first report: I do not think that “Team_Orangeworm” is the “Orangeworm” described by Symantec in their April, 2018 report, but so far, the hackers have not responded to a direct question on that point. As this situation evolves, I will update posts, as needed.