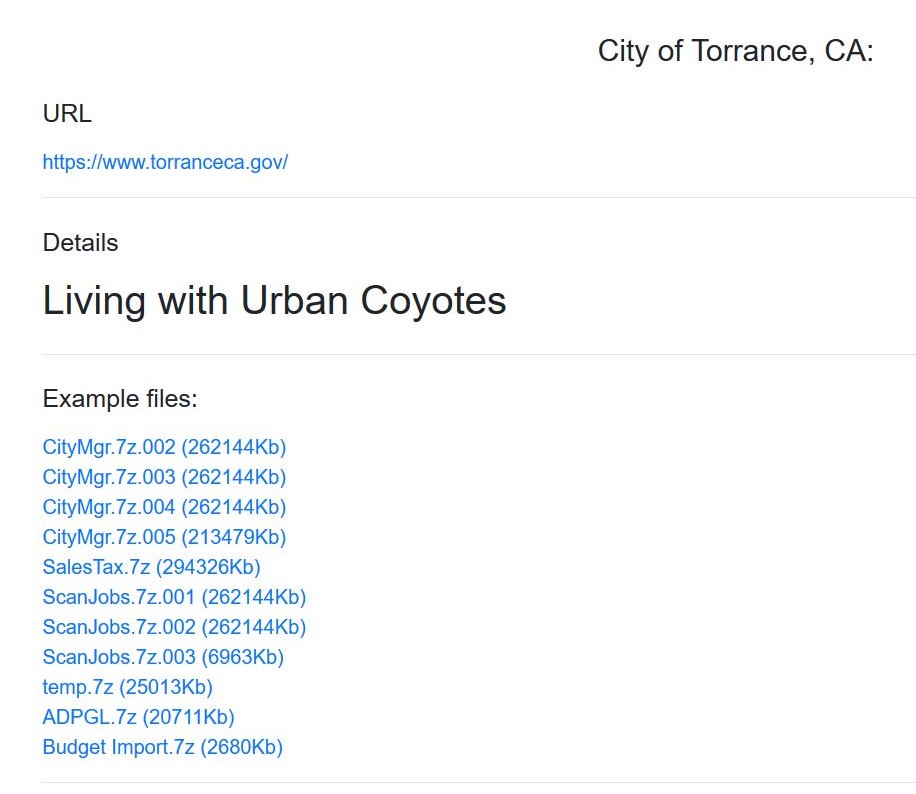
The DoppleLeaks site where DoppelPaymer ransomware attackers list victims who have not paid their ransom demands was updated this afternoon to includeTorrance, California as a victim.
There is nothing on Torrance’s web site about any attack and the city’s social media team did not reply immediately to an inquiry from DataBreaches.net has asking them if they could confirm the attack.
This post will be updated when more information is available.
Update: BleepingComputer was contacted by the attackers, who provided more details about the incident. You can read Lawrence Abrams’ reporting here.