The plastic surgery center of Dr. Kristin Tarbet in Bellevue Washington was not the only plastic surgery hit by ransomware on May 1. On the same day, Maze Team also reportedly hit Nashville Plastic Surgery Institute, LLC, dba Maxwell Aesthetics. It was the very day that they were reopening after having been shut down totally due to the city’s response to COVID-19.
As they did with the Tarbet proof, Maze Team dumped a lot of files with protected health information of patients. The patient information included name, date of birth, diagnostic information, type of surgery, and in some cases, health insurance information such as the patient’s policy number.
Even just a listing of the directory would have created problems for the practice, however, as they seem to use patients’ full names as part of the filenames. For example, one filename had the structure:
<last name> <first name> <type of surgery> <name of insurance company> <month> <year>.
That alone would probably require notification under HIPAA if it was simply exposed. But it wasn’t simply exposed. The unencrypted files in the data Maze dumped included details of patients’ histories that would warrant the planned surgery and authorization request from insurers.

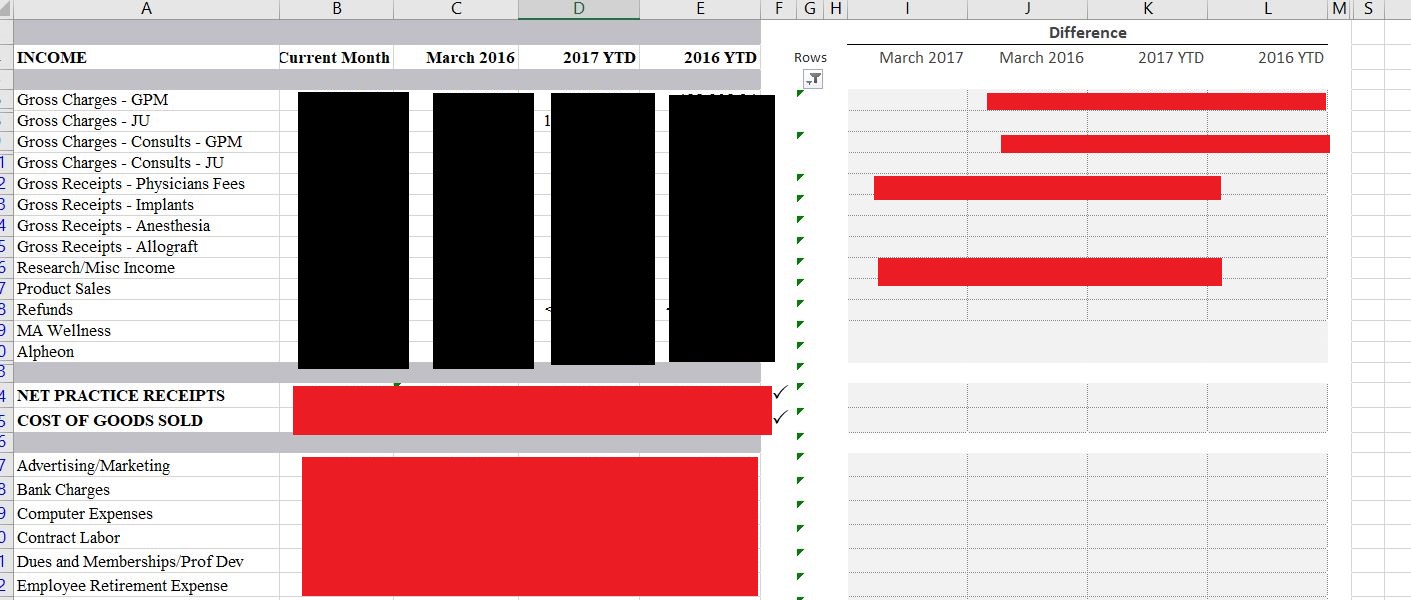
Other files also included orders for implants or extenders that would be needed for a named patient’s surgery. And yet other files related to business operations and network structure.
Given that two plastic surgery entities were hit on the same day, it may be that Maze hit a vendor or business associate, but that is not known at this time. The Maxwell Aesthetics website, which was online earlier this morning, is currently unreachable, and DataBreaches.net was unable to send them an inquiry at this time.
This may be updated as more information becomes available.