Last month, I pointed readers to a news report out of Moore, Oklahoma about how Tonya Smith, a former employee of Prime Communications, had reportedly been sent an email with personal information on 8,000 of their employees. The mistake occurred on December 11, 2019 after Smith had been terminated by Prime for performance issues. In response to her request for info on her 401k and employee profile, they reportedly accidentally sent her 105 pages of employee records that included SSNs, names, and dates of birth for thousands of their employees in a number of states.
That error is disturbing, of course. But what is more disturbing, perhaps, is that Smith claims that she notified them a number of times by both email and phone and they never responded.
“I emailed four or five times and I phoned three or four times,” Smith said.
After the media picked up the story on April 27 because Smith went to them with her concerns, Prime responded.
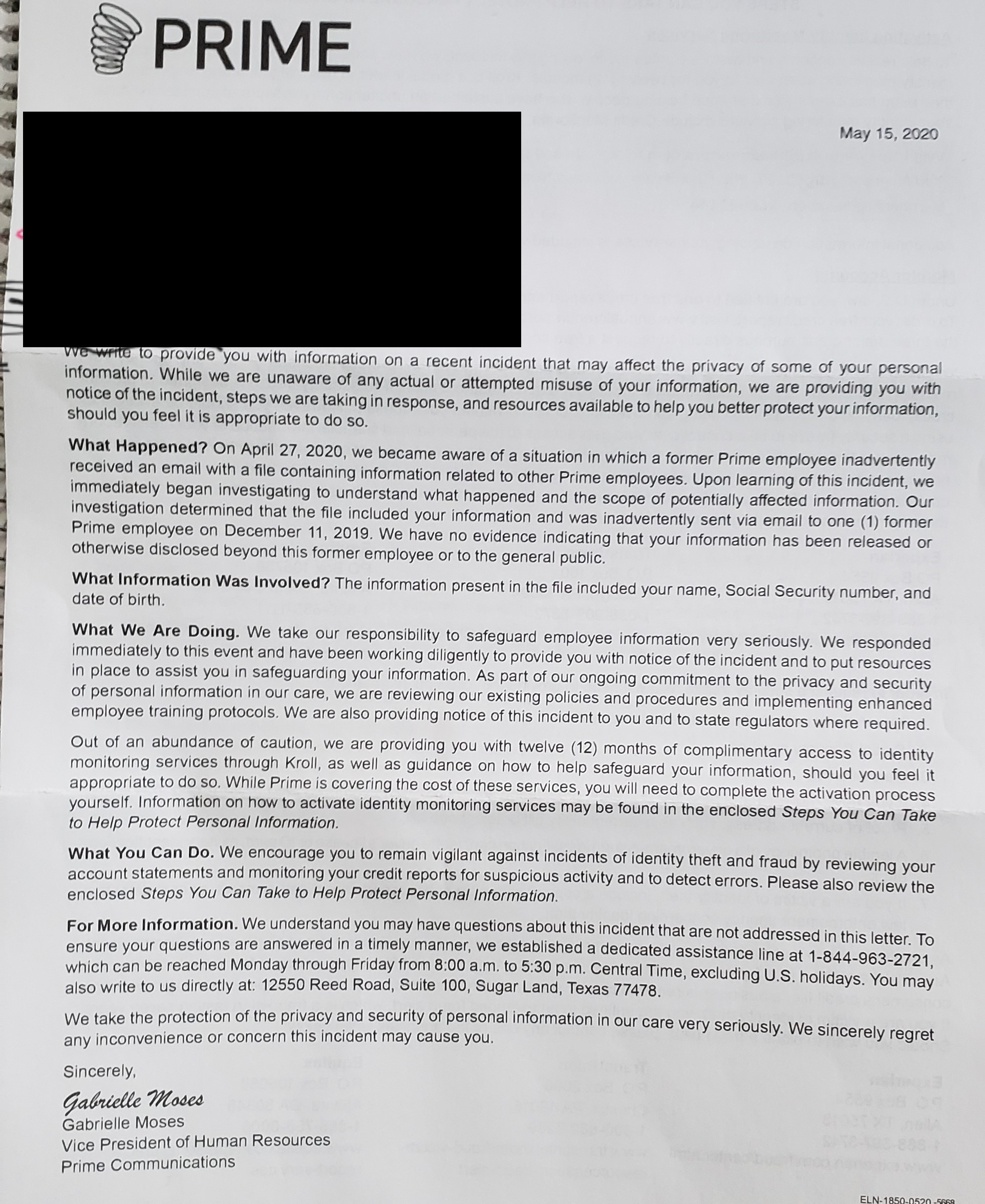
On May 15, Prime Communications, an authorized retailer for AT&T, sent a notification letter to those whose information was in the file sent to Smith. The letter, signed by Gabrielle Moses of Prime and sent to DataBreaches.net by a reader and former employee of AT&T, is reproduced below. It offers those impacted one year of identity monitoring through Kroll.
The letter predictably states that they have no evidence of any further distribution or any misuse of the data. It does not state whether the former employee had securely deleted their email with the file from her phone. It does not state whether anyone else had access to the phone. It does not state whether the former employee has securely destroyed any print-out. It does not state whether News4 in Oklahoma has retained a copy of the data obtained from Smith.
And it makes no mention of the fact that after their mistake on December 11, 2019, the former employee allegedly tried to notify them numerous times and they didn’t respond.
All their letter states is that “upon learning of the incident, we immediately began investigating” yada yada yada. No, Prime, you learned of the incident when your former employee emailed and called you beginning in December. Don’t make it sound like you had no notice before April 27 if you did but just failed to follow up on it.
In any event, in the wake of the incident, they are reviewing their policies and procedures and providing enhanced employee training. Hopefully that includes improving their incident response as to what to do when someone notifies them of a data security incident.