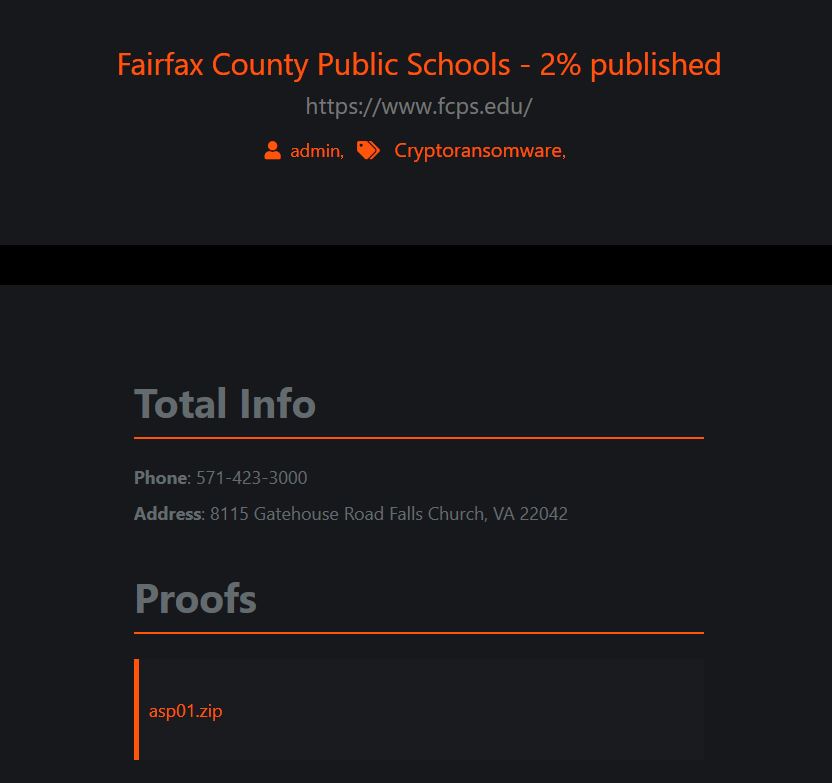
There was nothing on the homepage of Fairfax County Public Schools in Virginia that would indicate any cyberattack or problem, but the ransomware threat actors known as Maze had listed the FCPS on its leak site this week and provided some files as proof of access/acquisition.

DataBreaches.net contacted FCPS to ask them whether they would confirm the attack and to ask other questions. It took multiple attempts via multiple channels, but in response to this site’s inquiries, Lucy Caldwell, the Director News & Information for FCPS, has just responded:
We have just sent a note about it to all FCPS students/staff/families and posted it on our website:
https://www.fcps.edu/blog/fcps-statement-ransomware-investigationDue to the nature of the investigation, there is little information I am able to release other than this.
Indeed, the notice on their site does not provide any real details:
FCPS recently learned that ransomware was placed on some of our technology systems. We are taking this matter very seriously and are working diligently to address the issue. We currently believe we may have been victimized by cyber criminals who have been connected to dozens of ransomware attacks in other school systems and corporations worldwide. We are coordinating with the FBI on the matter.
At this time, our investigation of the issue is ongoing and we are working diligently to determine the impact of this incident on FCPS data. We have retained leading security experts to help us determine the nature and scope of the incident and recover from the situation.
FCPS is committed to protecting the information of our students, our staff, and their families. We will work with law enforcement to the fullest extent to prosecute any individuals or groups that attack our systems.
Fairfax County Public Schools
FCPS is a very large district — with 187,000 current students and approximately 25,000 staff. And that’s just current figures. It has not yet been made clear by the district or Maze whether Maze accessed and exfiltrated personally identifiable information on current or former students, current or former employees, and current or former parents.
Because Maze still has FCPS listed on their leak site, we can infer that FCPS has not paid ransom. Under the circumstances, if they dig in and refuse to pay, we should expect to see the threat actors dump more data. If that happens, hopefully the district will notify everyone promptly so that they can take steps to protect themselves.
In fact, if I was an employee or parent, I would assume the worst for now and take steps to protect myself and accounts. Employees may wish to consider putting a security freeze on their credit reports to prevent anyone from trying to pull a copy of their credit report. And parents and employees may wish to start regularly checking their banking and credit card statements for signs of suspicious activity. Hopefully, none of that will be needed, but better safe than sorry? In fact, regularly checking banking and credit card statements is just a smart practice in this day and age, so if you are not in the habit of doing those things already, why not start now?