Ross Kelly reports:
Critical services such as flood forecasting are still in operation, the agency said.
The Scottish Environmental Protection Agency (SEPA) has confirmed it is responding to an ongoing ransomware attack launched by a highly organised, international cybercrime group.
The cyber-attack was launched on Christmas Eve and has knocked a number of key systems offline since, causing great disruption for the government agency.
Read more on digit.fyi.
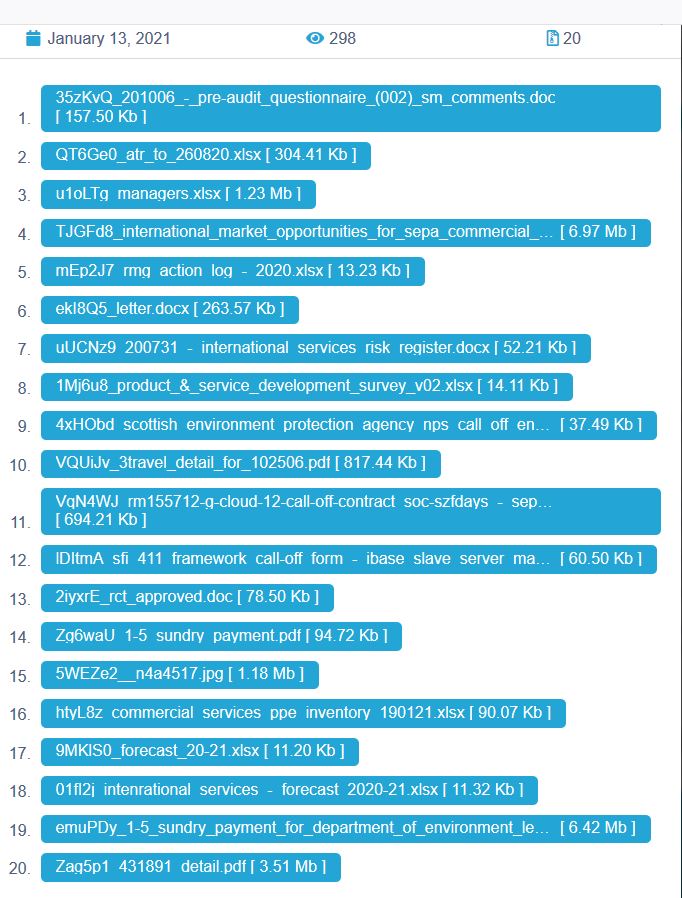
In this case, it is the Conti threat actors, and they have listed this attack on their dedicated leak site. Conti has dumped what they describe as 7% of the material that they have exfiltrated from SEPA — 20 files that do not seem to contain any particularly sensitive or personal information.
Many of the files would be publicly available if they have not already been publicly posted. But what else might Conti have exfiltrated? SEPA does not seem to know at this point.