As this site reported yesterday, Somerset Independent School District in Texas was reportedly attacked by Avaddon threat actors. Somerset has not responded to inquiries by this site and they do not seem to have posted anything on their web site about any breach.
Yesterday, the threat actors dumped an archive with 1,520 files in 27 folders. When uncompressed, there was more than 3 GB of data. Much of the data was from a few years ago, but there was a lot of personal and sensitive information about students.
As we’ve seen with other Texas k-12 districts, there were spread sheets with a lot of demographic information. The fields in just one of the plain text spread sheets consisted of:
- campus_id
- id
- fname
- lname
- password
- grade
- tstate_id
- tfname
- tlname
- gender
- race
- special_ed
- econ_disadvan
- eng_proficiency
- disability
- g/t
- homeless
- migrant
- ethnicity
- birthdate
There were more than 30 spreadsheets like the above from 2016-2020, with each spreadsheet having hundreds of rows/students.
There were also dozens of files revealing named students’ health issues. DataBreaches.net has redacted one such file from a prior school year for illustration purposes:
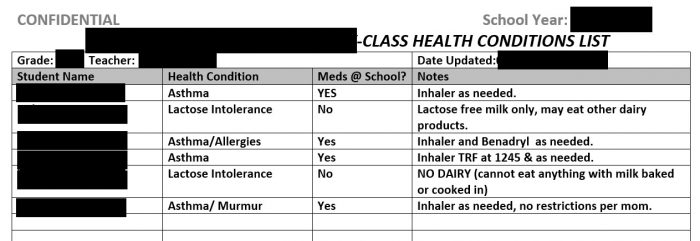
The files in the “Health” folder were for pre-K to Grade 4 classes.
At this point, the good news may be that the attackers have listed their entry as a “full dump,” suggesting that they have dumped all the data they had exfiltrated. Whether they are telling the truth is another matter. Did they get other data with personal information on staff and students? Hopefully, Somerset ISD will make some public disclosure soon about this breach.