Radixx, a subsidiary of Sabre Corporation, provides an air passenger ticket reservation system for low-cost airline carriers. On April 22, Radixx announced that Radixx Res™ had experienced a malware incident on April 20 that impacted its reservation system. The incident reportedly did not impact Sabre systems, and the customer database was not compromised. The incident did impact the ability of 20 customer airlines to book reservations, however, and Radixx hoped to restore services by the end of April 22.
Despite their best efforts, however, systems were still impacted, and on April 23, Radixx provided an update:
We want to further update you on Radixx’s recent incident as part of our ongoing communication efforts and the following information is subject to update.
We are starting to recover service to our customers and our teams are coordinating with customers throughout that process. In parallel, we will continue to provide support to our customers with their manual operations. We understand the urgency of the situation and are working to resolve the issue as quickly as possible. We regret the disruption this is causing.
Some of the airlines affected included Peach Aviation and ZIPAIR in Japan, as well as Air Belgium, Sky Airlines in Chile, Air Transat in Canada, Vietravel in Vietnam, Aero K Airlines in South Korea, Salam Air in Oman, FlySafair in South Africa, Air India Express, and Wingo in Colombia.
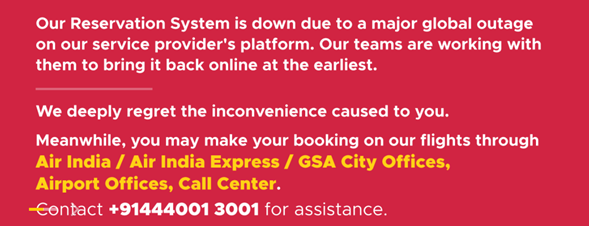
The service interruption made it imposible for many of the airlines’ passengers to make, change, delete, or confirm bookings through the airlines’ web sites, although flight operations were not affected. In some cases, like the Air India Express notice below, passengers were informed that they could call the airlines to handle their reservation needs.
In other cases, passengers were informed that if they needed to cancel a flight but couldn’t because of the service disruption, the airlines would give them a flight credit or some other arrangement to compensate them.
On some level, the service interruption may be the most serious for one of two start-up low-cost airlines. Avelo Airlines had just launched on April 8 and has its first flights scheduled for April 28.
As of the time of publication, airlines sites still carry the apology message and service appears to still be disrupted.
Reporting by Chum1ng0; edited by Dissent.