Rede Bahia, a Brazilian business conglomerate with16 multimedia vehicles focused on Bahia and Bahian people, was hit with a ransomware attack that impacted its functioning. As of today, the firm is still working to restore all functioning.
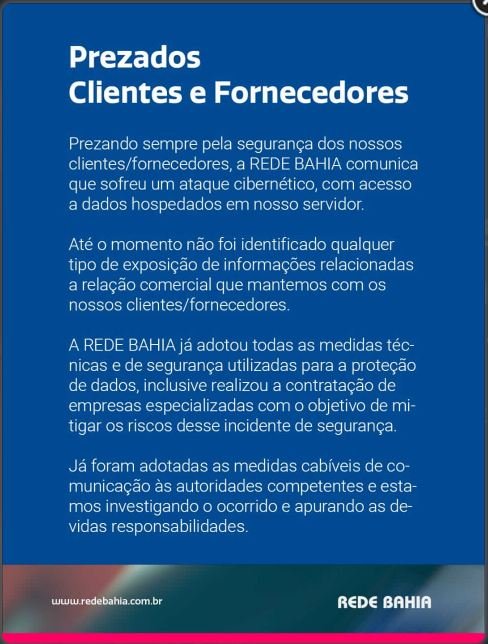
Notices about the breach were sent internally to employees, and posted publicly to others.
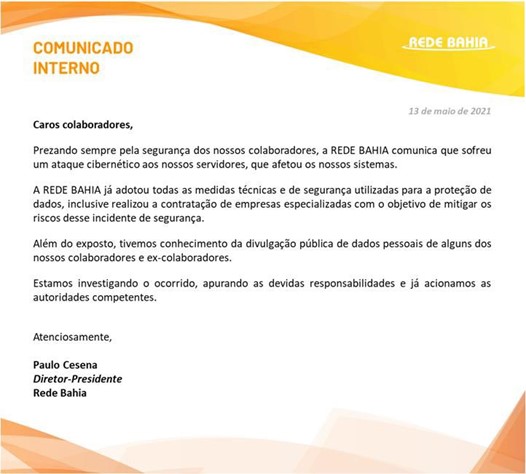
Translation of the internal memo to employees:
May 13th, 2021
Dear employees,
Always concerned about the security of our employees, REDE BAHIA communicates that it has suffered a cyber attack to our servers, which affected our systems.
REDE BAHIA has already adopted all technical and security measures used for data protection, including hiring specialized companies in order to mitigate the risks of this security incident.
In addition to the above, we became aware of the public disclosure of personal data of some of our employees and former employees.
We are investigating the occurrence, ascertaining the due responsibilities and we have already
the competent authorities.
Yours Sincerely
Paulo Cesena CEO Rede Bahia
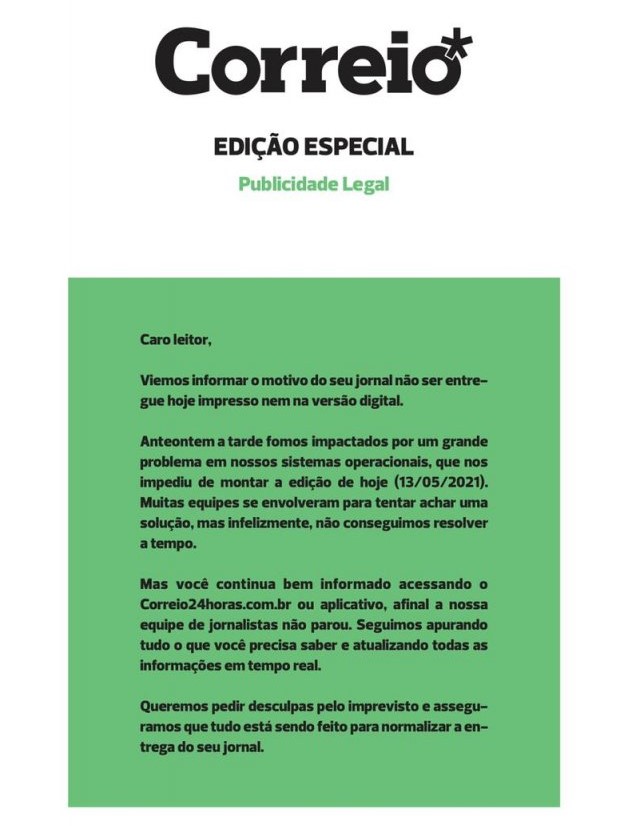
BNEWS confirms the cyber attack, that interfered with the daily publication of Rede Bahia’s newspaper, Correio. Rede Bahia posted notices where people could find all the news via radio or online while publication was disrupted.
While Rede Bahia noted that it was aware of leakage of some employee data, confirmation has been clear. BNEWS first posted, then silently deleted, a screencap of what appears to be redacted employee salary of some employees that was transmitted via email and posted on an unnamed social media account. The screen cap was then re-shared on Twitter.
DataBreaches.net is not posting it at this time because its authenticity has not been confirmed. Nor has the type of ransomware been reported or any ransom demand.
This post will be updated if more information becomes available.
Reporting by Chum1ng0 and Dissent; editing by Dissent