On June 9, Macaé issued a statement that it suffered a cyberattack. The following is a machine translation:
Macaé City Hall was the target of a cyber attack on the 3rd of June, the Corpus Christi holiday. Malware (a type of program designed to infect a user’s computer and harm it in various ways) has hit network file servers, systems and databases.
After verifying the invasion, the equipment was isolated to analyze the impact and type of malware. “Some important servers were infected and a lot of data ended up corrupted, leaving most of the internal systems unavailable”, informed the Assistant Secretary of Science and Technology, Marcos Lemos.
According to him, through network traffic verification it was possible to conclude that the virus arrived through the internal network (pendrive, local network or Home Office VPN) and not directly from the internet. The Macaé City Hall portal and the services available to the public through the internet were not impacted.
The City Hall, through the Assistant Secretary of Science and Technology, is working on the modernization project that will include investments in new computers for employees, security center, network management, cloud computing and other IT services to make management more efficient. and maintain a safe environment for the digitization of services to the population.
The Assistant Secretary of Science and Technology sent a memorandum to the Municipal Attorney General requesting that the necessary legal measures be taken. The document also requests that an incident report be made to the Police Office for the Repression of Computer Crimes (DRCI).
A statement on their Facebook page says:
Machine translation:
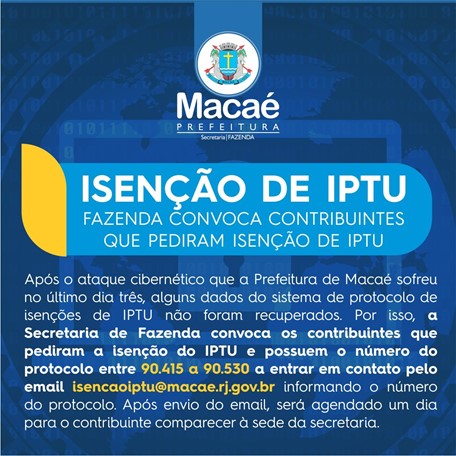
After the cyber attack that the City of Macaé suffered on June 3, some data from the IPTU exemption protocol system was not recovered. Because of this, the Secretariat of Finance calls on taxpayers who requested the IPTU exemption and have the protocol number between 90.415 and 90.530 to contact the Secretariat by email [email protected] informing the protocol number. After sending the email will be scheduled a day for the taxpayer to attend the headquarters of the secretariat.
The incident did not seem to have generated a lot of coverage, and the municipality has not appeared on any dedicated leak site that we have been able to find. It appears that despite the incident, the municipality went ahead with its focus and plans to vaccinate people against COVID-19.