Raphael Satter reports:
Hackers suspected to be behind a mass extortion attack that affected hundreds of companies worldwide late on Sunday demanded $70 million to restore the data they are holding ransom, according to a posting on a dark web site.
The demand was posted on a blog typically used by the REvil cybercrime gang, a Russia-linked group that is counted among the cybercriminal world’s most prolific extortionists.
Read more on Reuters.
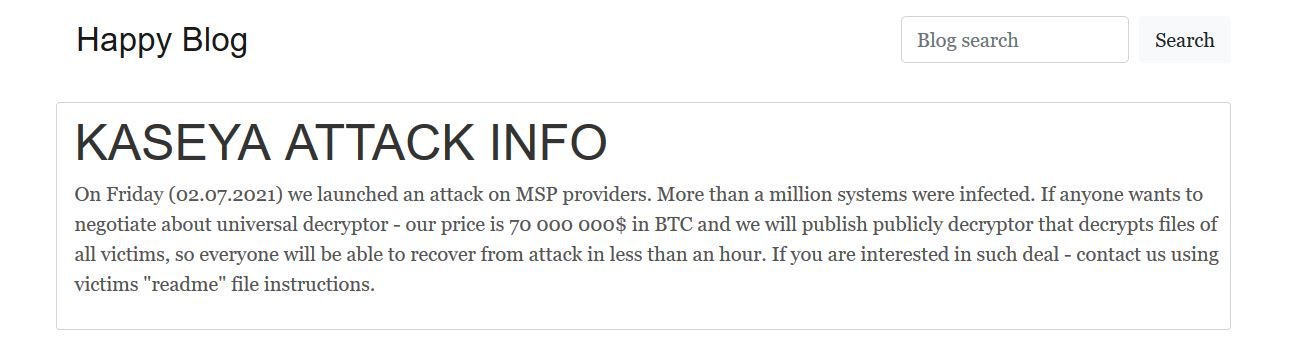
The message, depicted at the top of this post, reads:
On Friday (02.07.2021) we launched an attack on MSP providers. More than a million systems were infected. If anyone wants to negotiate about universal decryptor – our price is 70 000 000$ in BTC and we will publish publicly decryptor that decrypts files of all victims, so everyone will be able to recover from attack in less than an hour. If you are interested in such deal – contact us using victims “readme” file instructions.
Will anyone take them up on that offer, thinking that $70 million for so many companies impacted is worth it?