On July 9, the Royatonic spa in France suffered a ransomware attack. A notice on their web site informs people that as of July 12, the spa had to close because a cyberattack blocked access to their server and paralyzed all their activity.
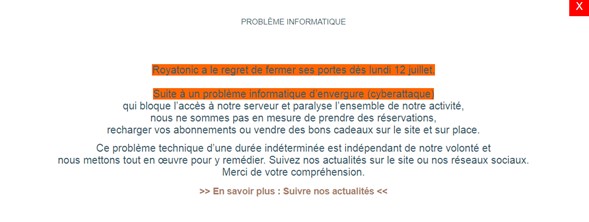
COMPUTER PROBLEM
Royatonic regrets to close its doors on Monday July 12th. Following a major computer problem (cyber attack) which blocks access to our server and paralyzes all of our activity, we are unable to take reservations, recharge your subscriptions or sell gift vouchers on the site and on site. This technical problem of indefinite duration is beyond our control and we are doing everything we can to remedy it. Follow our news on the site or our social networks.
Thank you for your understanding.
>> Find out more: Follow our news <<
Although they hoped to recover services quickly, as of July 15, the notice of closure is still up.
Francetvinfo obtained a statement from the director of Royatonic (translated):
A Russian hacker cryptolocked our server to us. It blocks our access to it. There is no data theft or hacking but we can no longer access our server. He asks us for a ransom to give us the key. We are lucky because we come across a hacker who plays in the 3rd division and asks us for less than a ransom bitcoin. Bitcoin is less than 28,000 euros. The ransom isn’t huge to make sure people pay.
We are in contact with him and at the same time we are implementing a plan B. The priority is to reopen Royatonic. We are at a standstill.
Despite the obvious stress of the situation, the director displayed a sense of humor. France Bleu reported that Dominique Ferrandon said:
In five days, I added a Russian hacker to my email contact list, I discovered new words like crypto-locked and I also looked at the bitcoin price!
Hopefully, the hacker has a sense of humor, too, and doesn’t take offense at being described as third tier.
On a serious note, Ferrandon noted that customer data was not at risk, and that they hoped to have the spa re-opened within 15 days. The following is a machine translation of her statement to Francetvinfo:
The priority option is reopening. We hope to do it in less than 15 days. We’d lose our client file. Usually, we welcome 300 people in snapshot over two hours. That’s about 1,200 people a day. It is a blow in the sense that it deprives us of activity for a fortnight. We lose turnover, but for 2 years we are used to losing.
Ferrandon added that they do not plan to pay the ransom but do not totally exclude the possibility:
On an ethical level, we would rather refuse to pay the ransom. On a purely logical level, it would also be no. We need to look at what consequences this can have on us in relation to the amount of the ransom.
Reporting by Chum1ng0, editing by Dissent