Grief threat actors have added another k-12 district to their list of victims who have refused to pay their ransom demands.
Greensville County Public Schools in Emporia, Virginia was added to Grief’s dark web leak site on September 21. But by September 15, the district had already disclosed that they were dealing with a cyberware attack.

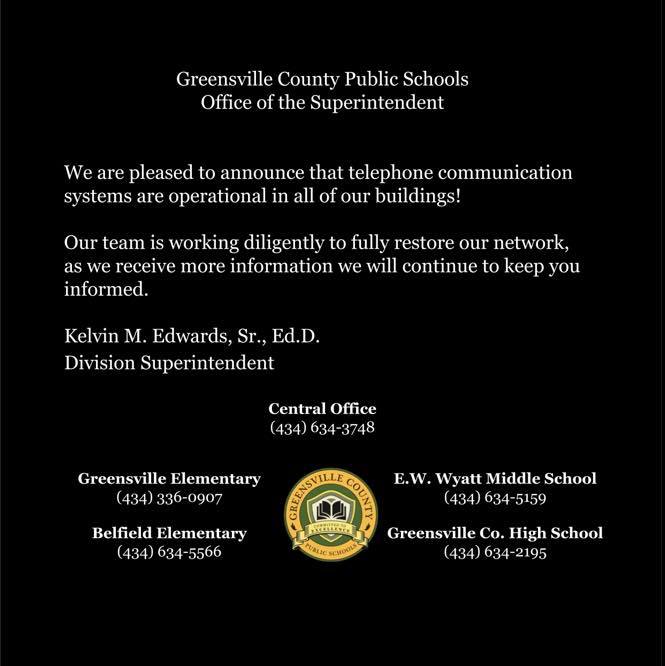
On September 16, an update posted by the district announced that telephone systems in all buildings were operational again and that further updates would be forthcoming as more information became available.
There do not seem to have been any updates since then.
About Greensville County Public Schools
Greensville County Public Schools is located in Emporia, Virginia. There are four schools in the district: Belfield Elementary School, Greensfield Elementary School, Edward W. Wyatt Middle School, and Greensville County High School.
On September 21, Grief dumped some data it had exfiltrated from the district. There were 4,604 .pdf files that all related to special education students or processes.
For those not familiar with special education: the federal government requires publicly funded districts to find and identify students with disabilities and to provide them with a free and appropriate public education.
To meet those goals under the Individuals with Disabilities Education Act (IDEA), districts conduct evaluations of students to assess whether they have a disability that impacts their ability to benefit from their educational program. If they do, a plan is developed that includes services (such as speech therapy, physical therapy, etc.), all at no cost to the student.
The thousands of files that Grief dumped related to special educational evaluations, plans, and processes for students in the district’s schools. The files were date-stamped from 2017 and 2018. The student records contained differing information on each student, but generally included the student’s name, address, phone number, parent or guardian’s name, and then information on the child which might include a medical or social history, the results of education or psychological testing, and any other materials relevant to evaluating a student, developing a plan for them, or evaluating the student’s progress under the plan. In some cases, the files were district refusals to provide services or to change a plan, with an explanation as to why.
DataBreaches.net did not see any employee personal information in the data that have been dumped so far, and the district did not responded to email inquiries yesterday asking whether any employee or personnel information had been accessed or acquired. This post may be updated if a reply is received.
Other Districts Hit by Grief
Grief threat actors have been described by others as being a possible rebranding or evolution DoppelPaymer. Grief is also thought by some to be part of Evil Corp, a Russian-based group that is on the Treasury’s sanctioned list, which means that victims run a serious risk if they make any ransom payments to a sanctioned entity.
Other k-12 districts hit by Grief this year include:
- Clover Park School District in Washington State
- Lancaster Independent School District in Texas; and
- Booneville School District in Mississippi
If Grief follows their usual pattern, they will dump more data in stages.
Grief has recently issued a statement agreeing with Ragnar_Locker threat actors who have started threatening victims that if they go to the FBI or use recovery firms, the threat actors will just dump all the files publicly. Grief has gone even further with its threats, however, threatening to just destroy all the data so that the victim can never recover it. Whether these groups will follow through on their threats or such threats will become more common remains to be seen.
Additional research provided by Chum1ng0