On September 25, DataBreaches.net reported that GrupoGSS, a division of Covisian, had been the victim of a ransomware attack by Conti. In a statement to DataBreaches.net, Covisian confirmed the attack but also stated:
We hereby confirm that neither GSS nor Covisian have conducted negotiations of any kind with anyone regarding the cyberattack.
Their firm denial, which we reported at the time, seemed in conflict with a chat log involving Conti and what appeared to be a negotiator for or representative of GrupoGSS or Covisian (names are not used in the chat window between a ransomware group and their victim).
For a few days, someone who appeared to be representing GrupoGSS or Covisian was telling Conti that they would pay $8.5 million, but could Conti please break it up into 100 different BTC addresses:
We would like to do one small request sir, can we split the money into smaller amount Example : 8500000$ 100 times in 100 different addresses. To maintain our financial books, we don’t want to be get caught by tax or auditing department to hide these transactions, we need your help. It’s a humble request We will pay the network fee whatever it will be
I hope you understand our situation.
Conti agreed to that and began generating BTC wallets for them to use. The negotiator also had another request:
sir one small request kindly delete this chat. We don’t want that our name has been seen by anyone and it’s malign our reputation. This chat contains some sensitive information. I hope you understand. It’s a humble request
Conti responded:
Sure, we will delete it as soon as we receive payment and provide required information to you.
To all appearances, then, what appeared to be a negotiator for GrupoGSS/Covisian had struck a deal with Conti to pay them ransom. Note that while there was nothing in the chat log that clearly indicated that the victim was GrupoGSS, the victim uploaded a test file so that Conti could prove that their decryptor worked. That file, still available online, when decrypted contained code that included:
-<RegistrationInfo>
<Date>2018-07-10T17:04:39.2564211</Date>
<Author>GRUPOGSS\administrador</Author>
</RegistrationInfo>
So the “victim” had access to files that had been encrypted by Conti and that contained at least one reference to GrupoGSS.
While the speed with which the negotiator readily accepted all terms and kept calling Conti “Sir” seemed a little suspicious to some, there was some indication that this was a real negotiation — or at least a real negotiator who might have been stalling for time while the firm tried to recover from backup.
Confronted with Covisian’s firm denial of any negotiations at all, DataBreaches.net followed up with a question:
So that chat log snippet I sent you concerning payment of $8.5 million did NOT involve someone negotiating for GrupoGSS or Covisian, even though the decrypted file linked to GrupoGSS?
They never answered that question.
But shortly after agreeing to pay, the victim suddenly went quiet. Apart from one “hello” the next day, did not respond to further contacts from Conti.
Did the publication of the first chat snippet on Twitter by an intel group spook GrupoGSS from negotiating?
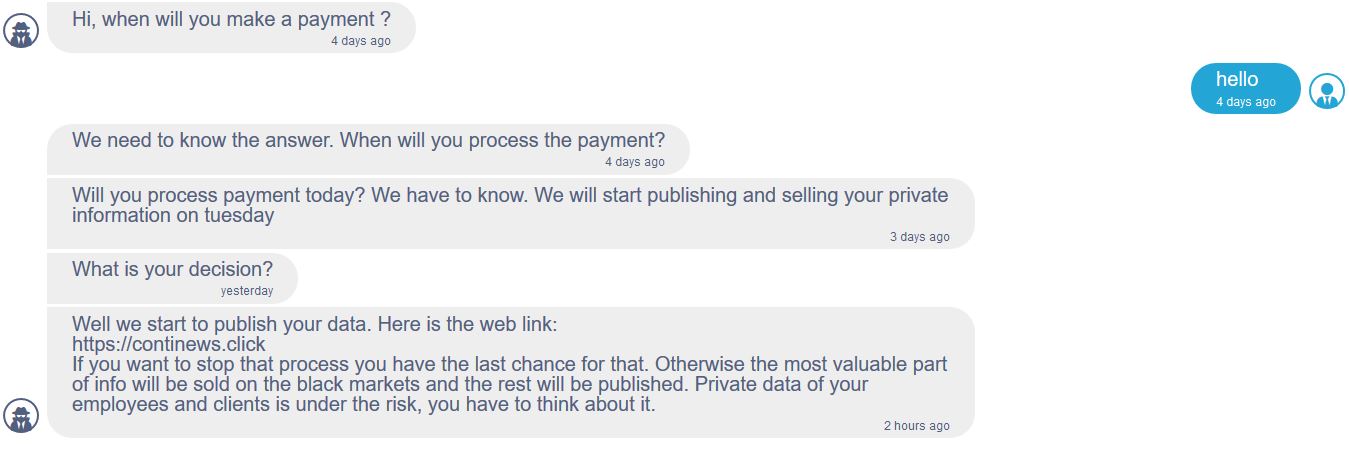
Yesterday, and as indicated in the chat log in the screencap above, Conti started dumping data.
DataBreaches.net contacted Covisian again to ask them if they wanted to change or update their statement denying any negotiations. They have not replied.
The dumped files (approximately six dozen as a preliminary dump) contain at least one file that appears to have personal data on employees. Covisian’s statement of September 25 had stated that there had had been no evidence of leakage of any personal data. They may need to revise that statement as more data becomes available.
Additional help provided by Chum1ng0