The Desorden threat actors have been busy, it seems, as they have announced an attack on Central Restaurants Group (CRG) in Thailand.
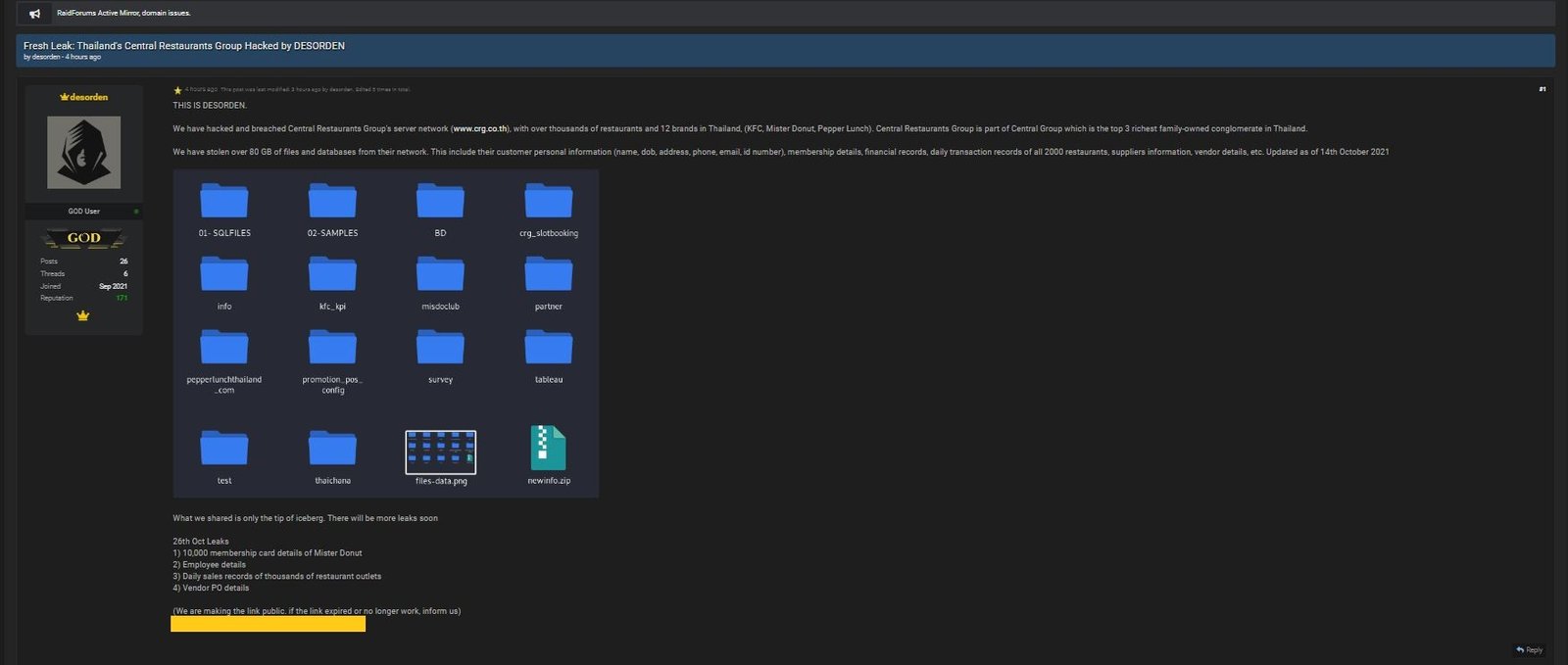
The attack, with proof of claim, was posted on a popular hacking forum and sent to DataBreaches.net. The proof of claim files included membership card details of Mister Donut, employee details, daily sales records of what they describe as thousands of restaurant outlets, and vendor purchase order details.
The employee-related spreadsheet contained more than 2000 records with fields that included: emp_id, perface_id, thai_fname, thai_lname, eng_fname, eng_lname, username, nickname, email, and phone number, as well as other details.
CRG is linked to a number of popular restaurant brands, including Mister Donut, Kentucky Fried Chicken, Auntie Anne’s, ColdStone Creamery, and others.

An email sent to the firm’s data protection office this morning asking them whether they would confirm the claimed attack was not immediately returned. This post will be updated if or when a reply is received.