In July, this site noted a May, 2021 ransomware incident that significantly impacted Florida Heart Associates. In July, they notified HHS that 45,148 patients were impacted.
Now this week, we learned that it was Pysa threat actors who had attacked them, and they have now dumped some of the data.
Pysa’s dump is a little puzzling as it would suggest the threat actors had broken up the data into almost 40 parts (at least) and yet only 3 parts have been dumped (at least as of today). Those parts contain thousands of files, many with protected health information.
Evidence of encryption was also spotted:

But confusingly, there was more than one kind spotted:
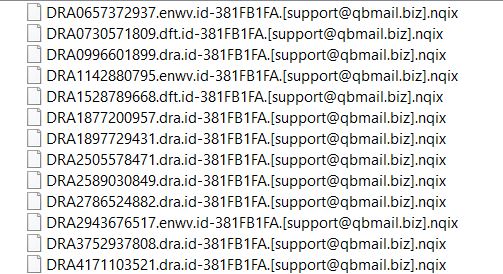
Brett Callow of Emsisoft informs me that both of these are Dharma.
But did Pysa use two different types of ransomware on Florida Heart Associates or was there an earlier attack that we are seeing evidence of?
DataBreaches.net sent an inquiry to Psya asking them if they could clarify whether they used one or two types of ransomware, and if (only) one, which one of the two was theirs? An email inquiry was also sent to Florida Heart Associates last night asking them to clarify what happened.
Neither inquiry received any answer by the time of this publication. This post will be updated if one is received.