Unauthorized access to a New Jersey Health Information Management (HIM) vendor’s portal has resulted in some patients’ protected health information being acquired and exfiltrated.
Earlier today, DataBreaches was contacted by someone known to this site as “DarkFox.” DataBreaches has reported on DarkFox in the past without identifying them, but is identifying them this time by agreement.
According to information and screencaps provided exclusively to DataBreaches, DarkFox acquired and used login credentials to access the client portal for Clairsol Inc. Those credentials enabled DarkFox to access records from state-run medical facilities in New Jersey, including the Trenton Psychiatric Hospital, Ancora Psychiatric Hospital, Greystone Park Psychiatric Hospital and two other facilities.
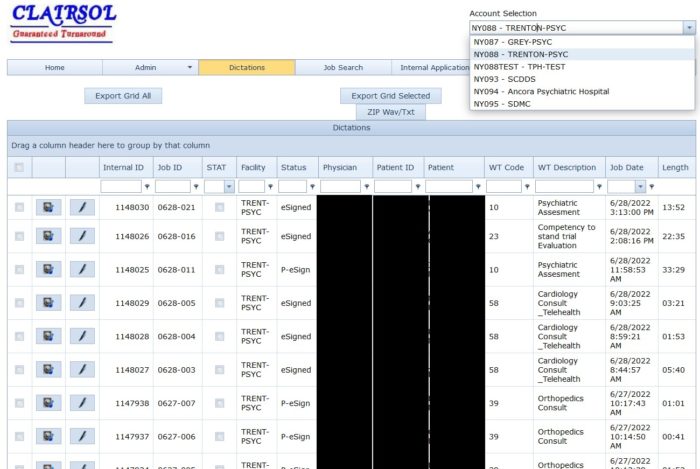

Patient information in the second screencap above corresponded to data in the first screencap, but the spreadsheet contained more data — 4152 rows. The 4,152 rows do not represent unique patients, however, as there were multiple appointments or assessments for some patients.
On inquiry, DarkFox explained that they found the login credentials in plain text in a file on a computer they were scanning. DataBreaches does not know whether the computer belonged to a provider or an employee of Clairsol or some other individual. But DarkFox emphasized that the credentials were in plain text and that they provided access to Clairsol without any second factor or multi-factor authentication required.
“Just user and pass and bam in,” DarkFox told DataBreaches.
After quickly determining that the data appeared to both real and current, DataBreaches.net called Trenton Psychiatric Hospital. Asking the switchboard to be connected to cybersecurity for the hospital resulted in an actual person picking up the phone who not only immediately grasped the situation but escalated it immediately to their administrator who then called DataBreaches. As DataBreaches understands the situation, within minutes of our phone call, the administrator was instructing all of their providers not to use the portal until further notice. This post will be updated when DataBreaches receives any update or follow-up from Trenton Psychiatric Hospital’s HIM administrator.
Yet Another Transcription Service Also Compromised?
At about the same time DarkFox was giving DataBreaches info on the Clairsol breach, they also posted other credentials on a popular hacking forum. In their post, they provided a New Jersey Department of Health & Services login to the client login portal for Transriter. Those login credentials had not been used since 2019, according to DarkFox, but still worked. DataBreaches was able to determine that the provider associated with those credentials had been a psychiatrist associated with the state hospital.
Although the credentials were no longer used, it appears that they were never disabled by Transriter. Patient records that DarkFox was able to access were uploaded to the forum where they were made freely available to everyone.
Coincidentally — or perhaps not — Transriter™ is a medical transcription and document platform that is built, owned and supported exclusively by Diskriter.
If the name Diskriter seems familiar, it may be because last week, DataBreaches reported that Diskriter had been hit by the Hive ransomware group on June 8.
Doing the Right Thing
Although DarkFox posted some sensitive Transriter data on a forum, and although they had acquired sensitive information on patients via the Clairsol portal, they did not post the login to Clairsol or leak any patient data from the Clairsol portal.
To DarkFox’s credit, after communicating with DataBreaches, they agreed not to leak the Clairsol data at all.
The fact that the data are not being leaked publicly is a relief, but it does not negate the covered entity’s obligation to evaluate whether this was a reportable breach under HIPAA, and if so, to make the required notifications. DataBreaches would think that notifications are required because protected health information wound up in unauthorized individuals’ hands.
But apart from the notification issue, it appears two HIMs have recently been compromised: Diskriter and Clairsol. Diskriter allegedly had 160 GB of data stolen, and their server(s) encrypted. Clairsol had a very limited amount of data exfiltrated but had no MFA on its client login portal. This might be a good reminder for covered entities to audit or review the security protocols their HIM vendors have in place.