After weeks of information and misinformation leaking out, and after some outstanding reporting by Valéry Rieß-Marchive on LeMagIT, LockBit 3.0 has publicly confirmed that they are responsible for the attack on South Francilien Hospital Center (CHSF).
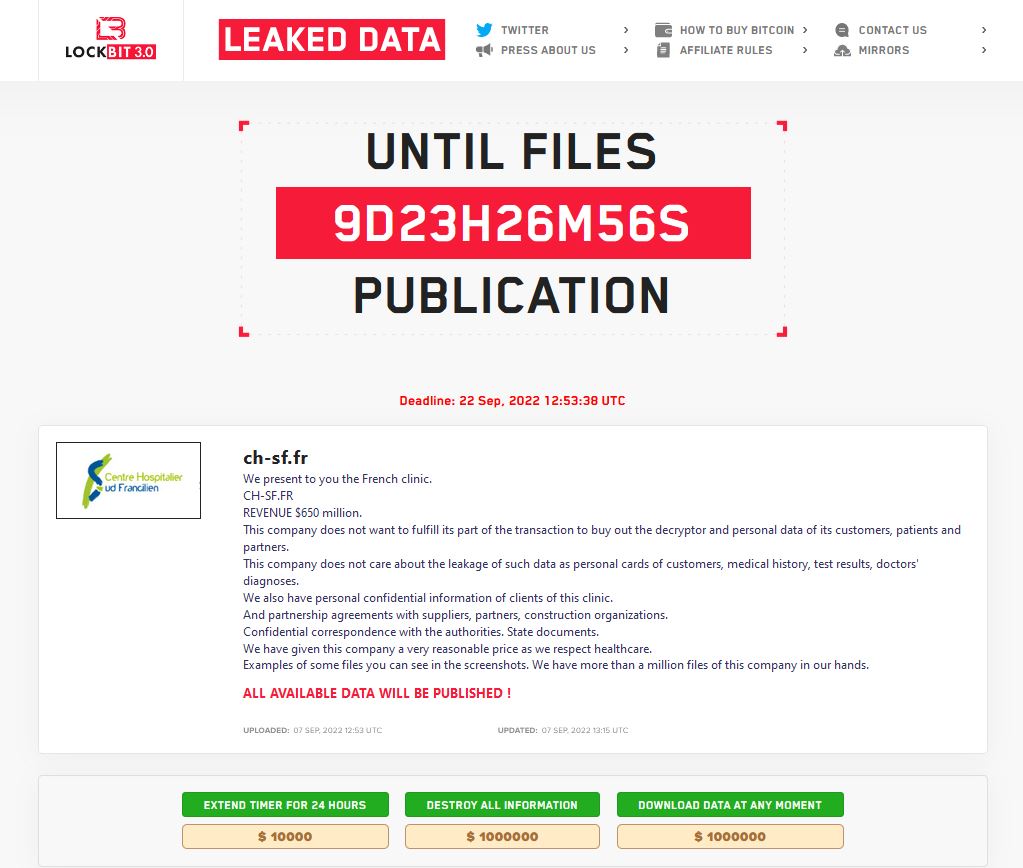
Consistent with the usual rhetoric we see from threat actors in such circumstances, LockBit tries to put responsibility on their victim, and claims “We have given this company a very reasonable price as we respect healthcare.”
The extortion demands are $10,000 to delay publication for 24 hours more; $1 million to destroy all the data, and $1 million to buy all the data. Claims that the original demand was $10 million were inaccurate.
LockBit claims to have more than one million files from the hospital.