JAKKS Pacific, Inc. describes itself as leading designer, manufacturer and marketer of toys and consumer products sold throughout the world. The firm is headquartered in Santa Monica, California. Its proprietary brands include Fly Wheels®, Perfectly Cute®, ReDo Skateboard Co.®, X Power Dozer®, Disguise®, Weee-Do™ and a wide range of entertainment-inspired products.
On December 8, JAKKS became the victim of not one, but two, ransomware teams. Their data was locked by Hive and it was also locked by ALPHV (BlackCat). According to a statement by Hive’s spokesperson to DataBreaches, the two groups agreed on one price they would split if JAKKS paid: $5 million. But also according the spokesperson, JAKKS did not negotiate at all.
On December 19, Hive started leaking data they had exfiltrated.

On December 28, BlackCat added JAKKS to their leak site.
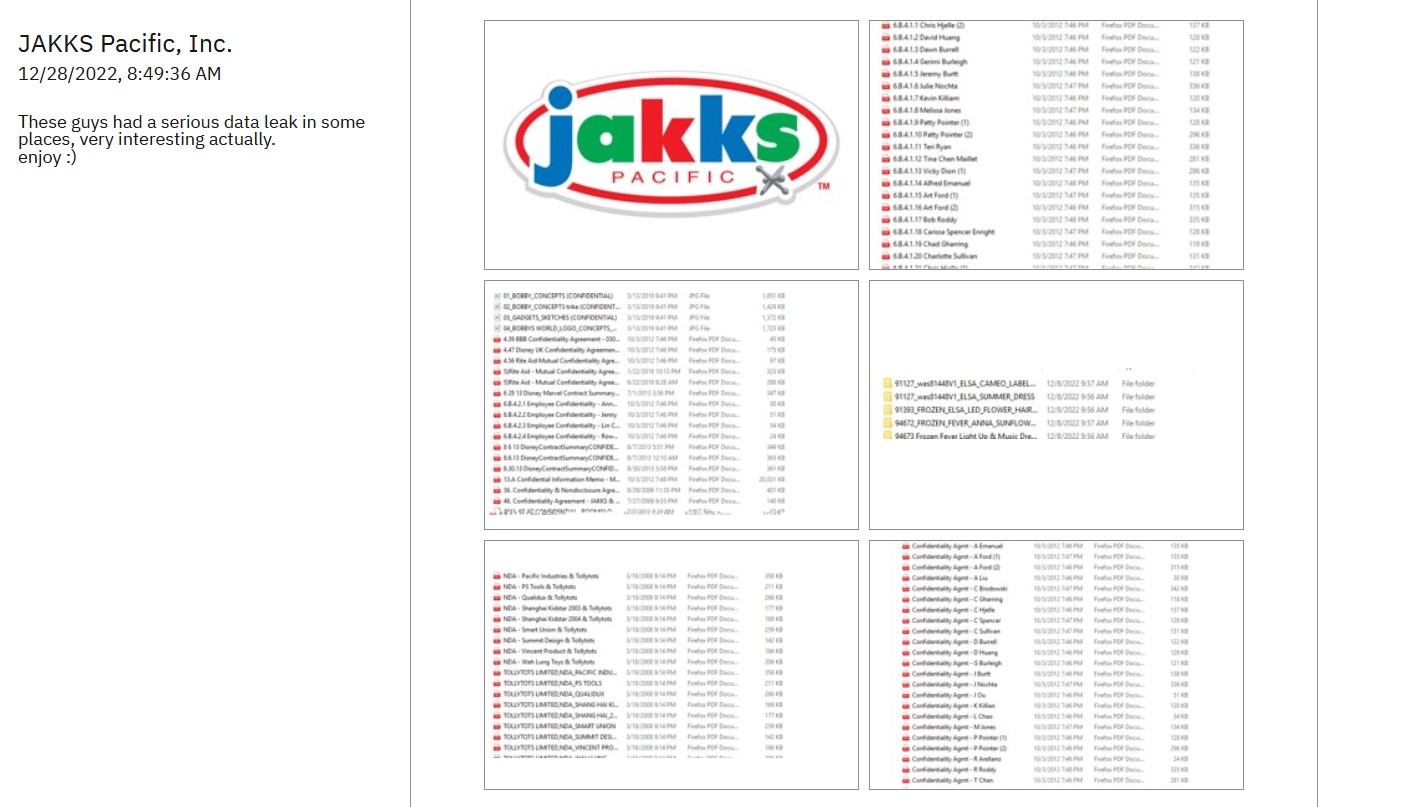
BlackCat attached five screencaps of directories as proof but have not leaked any actual files as yet.
DataBreaches asked Hive how they and BlackCat wound up locking JAKKS on the same day. Their spokesperson stated that both groups had bought access to JAKKS from the same internet access broker or affiliate.
JAKKS Responds to the Incident
On December 22, JAKKS posted a notice on its website:
Notice of Recent Cyberware Attack – December 22, 2022
On December 8, 2022, JAKKS experienced what many other companies have been and are experiencing: a ransomware attack by bad actors who inserted malware into JAKKS’ computer network and locked up our servers.
We promptly retained cyber forensics specialists who are actively investigating the incident, helping to restore our servers, taking steps to prevent a recurrence, and utilizing additional security measures to help safeguard the integrity of our system’s infrastructure and the data contained therein. Our Form 8-K describing the event was filed on December 15, 2022, and can be found at https://www.jakks.com/investors/sec-filings.php.
We believe that the data that was unlawfully accessed potentially includes personal information (including names, emails, addresses, taxpayer identification numbers, and banking information of affected individuals and businesses).
We suggest that you immediately take appropriate protective measures to safeguard your personal and banking information.
This is an ongoing investigation. JAKKS regrets any inconvenience this incident may cause. Be assured that we have been and will continue working diligently to protect the security and confidentiality of the information contained in our computer network, as we get our network up and running.