The CL0P ransomware gang has added the NYC Bar Association to their leak site today.
Unsurprisingly, the threat actors have some unkind words for their victim:
The New York City Bar is example of one more institution who not take their obligation to secure client, employee and case data seriously. We download more than 1.8tb of data and now is time to have some lawsuits started and fines for neglecting their duties. Every single system was locked back in mid-December yet the organization said nothing to anyone to try and keep it all under wraps. Data size is so large we have to share over some weeks.
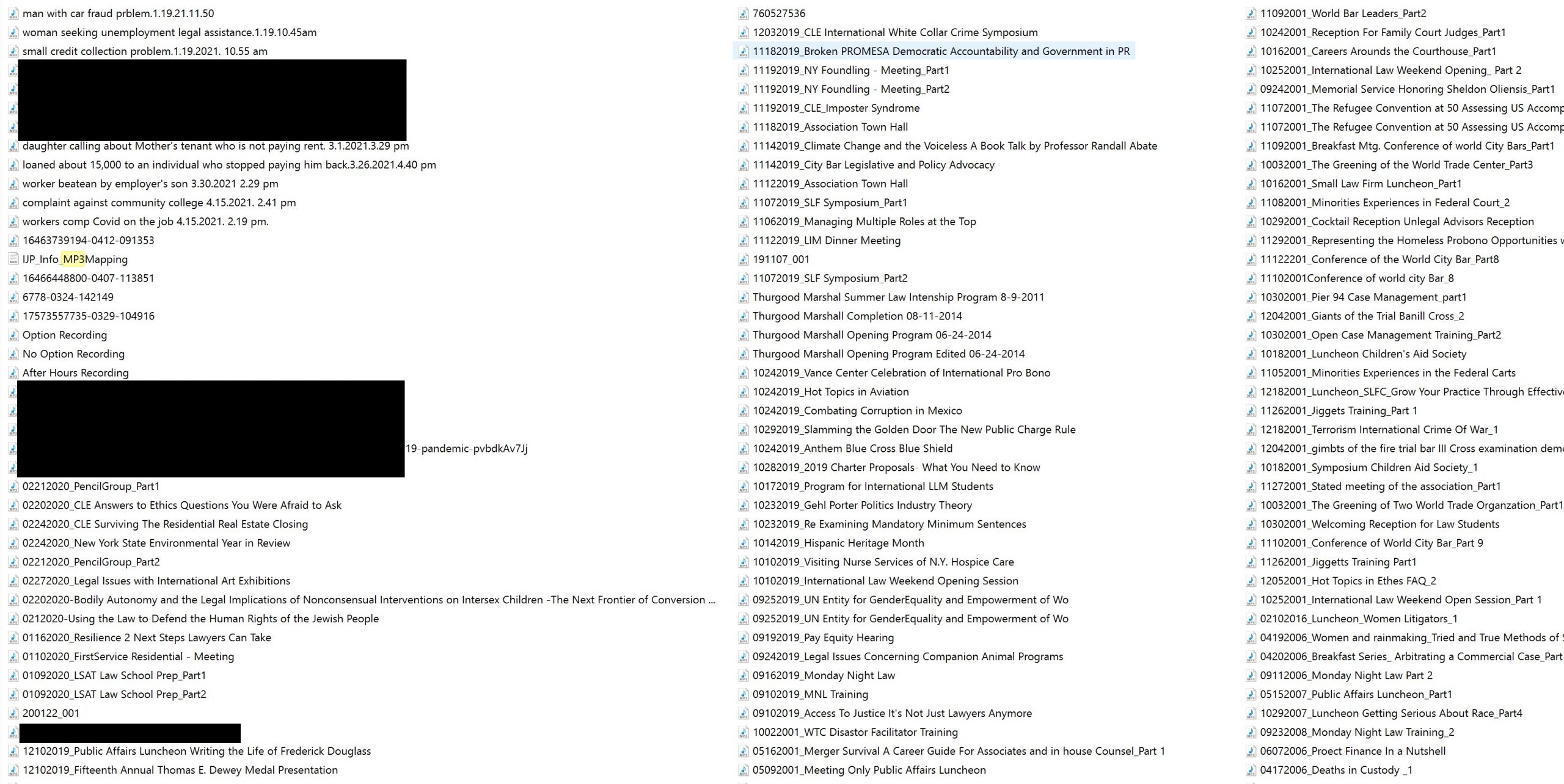
As proof of claims, CL0P provided a screenshot of a portion of a file directory, redacted by DataBreaches.
In addition to the above, CL0P also posted screenshots of passports for a number of individuals. Why the NYC Bar is in possession of those passports was not made clear on the leak site.
DataBreaches has sent an email inquiry to the NYC Bar Association asking them about CL0P’s claimed attack and whether they have made any notifications to regulators, employees, or individuals whose personal information was accessed or acquired, but no reply was immediately available.