The Council of Granada is a public entity providing direct services to citizens as well as technical, economic, and technological support to the city councils of the municipalities of the province of Granada, Spain.
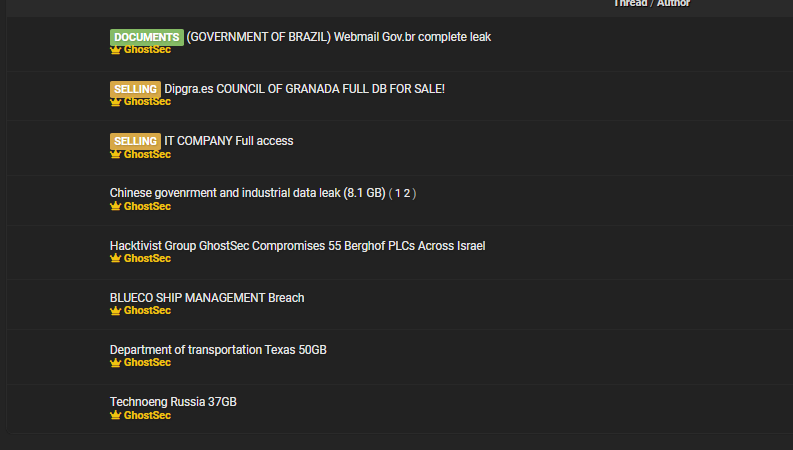
On December 29, 2022, the group known as “GhostSec” listed a Granada Council database at dipgra.es for sale, claiming they had almost 7 GB of information. A small sample was provided as proof. The group signed their listing, “~With love GhostSec <3”

The database was listed with a price of $450, but one month later, it had not sold. On January 29, people on Twitter started paying attention to the listing. A few days later, a story in IDEAL.es also covered the story, reporting that the council claimed that they had implemented all protocols and this was a minor incident (the news report is behind a paywall).
GhostSec posted a second sales listing on their Telegram channel on February 11 with an asking price of $450.00. On February 16, they lowered the asking price to $250.00. The listing was subsequently deleted and GhostSec informed DataBreaches that they had sold the database.
The Data Sample
DataBreaches examined the data sample provided and found 17 folders. Some contained acronyms corresponding to institutions that have to do with the deputation of Granada, such as campus_social, a subdomain of the deputation of Granada, Cemci (The Center for Municipal Studies and International Cooperation), and pmd (Granada Sports Council). The sample contained personal and work-related information on individuals.

Several files in the sample also contained usernames and passwords.
On February 15, DataBreaches sent an inquiry to the council asking specifically about the usernames and passwords. Getting no reply (although the council later informed us that they had replied to our earlier inquiry), DataBreaches sent a second inquiry on March 2.
When asked whether the incident had been controlled (as the council had reportedly claimed in early February), Amina Nasser Eddin, the council’s Directora de Prensa, wrote to DataBreaches, “Yes, we have detected the vulnerabilities and have proceeded to resolve them.” It is not clear to DataBreaches whether they are claiming that they are no longer susceptible to an SQLi attack, which is how GhostSec told DataBreaches they had gained access.
In answer to a second question from DataBreaches about the accounts with usernames and passwords, the council spokesperson replied, “There are accounts that are old and have not been in force for years and the current ones have been disabled and have been renewed.”
According to GhostSec, the data, which included many passwords not disclosed in the sample, was acquired from dipgra.es in late December. The council never contacted them about the listing, GhostSec claims, and they never contacted the council. But now the data, including data that DataBreaches has not seen, is in the hands of an unknown buyer.
GhostSec
GhostSec joined Breach Forums in June 2022, but they are not a new group. GhostSec, who has been described by others as hacktivists, rose to prominence through their attacks on pro-ISIS entities. They have also embraced other causes, such as #OpIran.
At times, they have been affiliated with Anonymous. At other times, they have tried to distinguish themselves from Anonymous. In a March 2022 tweet, GhostSec listed their member accounts: @SebastianDAlex @YounesAnonymous @wond3rghost @YourAnonWolf @Denrow1337 @shdwpnda @squad3o3 @An0nAKn0wledge
DataBreaches hopes that Granada’s council is right and that they have controlled the incident and taken care of any passwords that might have still been working at the time of the attack.
Some additional material and editing by Dissent.