Cementos Bío-Bío S.A attacked by BlackByte
Cementos Bio-Bio S.A, a Chilean cement company, was added to BlackBye’s leaks site on April 9.

DataBreaches found no notice of any incident on the main cbb.cl website, but the cbbexpress.cl customer portal had a notice about interruptions: “At this time we are having intermittencies with our services. If you have any questions or queries, please contact the executive.” The notice no longer appears on the portal.
Attempts to seek confirmation and details from CBB via their Facebook account on April 10 and via email to an executive on April 11 both failed to receive replies. When contacted on April 10, BlackByte Support confirmed that they used encryption in this attack. In response to other questions, they informed DataBreaches that they had exfiltrated about 200GB of files. CBB had not responded to them at all or attempted to negotiate, they said.
MX: BlackCat claims attack on the Yucatan government
On March 31, DataBreaches reported that the Yucatan government had confirmed a cyberattack. Since then, BlackCat claimed responsibility for the attack and posted some data as proof including samples of INE documents (electoral documents related to voting eligibility) in addition to a letter of commitment from the Yucatan state government.
DataBreaches emailed the Yucatan government to ask if they knew what information had been stolen and if citizen information was involved. We have not received a response from them.
BlackCat did not respond to inquiries as to how much data they exfiltrated and if there were any negotiations with Yucatan.
PE: Group Euromotors attack claimed by LockBit
The Peruvian company Euromotors is dedicated to the sale of new and used automobiles, maintenance services, and the sale of original spare parts. Euromotors is made up of a group of 12 companies: Euromotors, Euroshop, Altos Andes, Euro Camiones, San Bartolomé, Eurorenting, Euroinmuebles, One, Eurolift, Revo Motors, Euroconnect, and International Camiones del Perú.
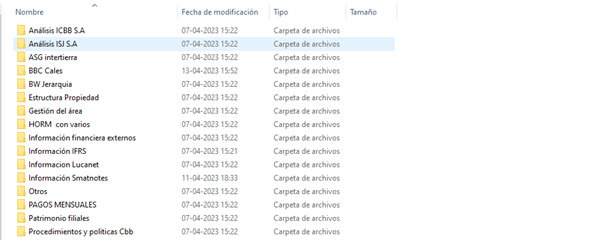
Euromotors was added to the LockBit leak site on April 10 without any sample data or tree file. LockBit listed prices of $5000 to delay the publication of data, and $500,000 to destroy all information or download all the data. On April 17, LockBit dumped information in two files: one a sample in 7z format (144 MB), and the other a file tree list.
The sample contains folders with email names belonging to the Euromotors group and some personnel information such as vaccination cards, COVID tests, and a database of employees with personal information. Internal corporate documents were also leaked.
DataBreaches could find no disclosure by Group Euromotors on their site or social media. Emails sent to them on April 10 and April 12 requesting information on their incident response went unanswered. An email sent to them earlier today also did not receive any reply.
CL: Apro.cl attack claimed by LockBit
Apro Ltda is a company that sells personal protection and industrial safety items. Apro.cl, which has stores throughout Chile, was added to LockBit’s leak site on April 13 without any sample or file tree. For $1000, people could delay publication of the Apro data for 24 hours. For $199,999, people could delete or download all the data. As of today, LockBit has not leaked the data.
Because we could find no notice on Apro’s website or social media accounts, DataBreaches sent email inquiries to Apro on April 13 and April 15, asking them when the attack occurred and whether they had negotiated with LockBit at all. No reply has been received.
MX: National Water Commission hit by BlackByte
Mexico’s National Water Commission (Conagua), which manages, protects, and controls national waters in Mexico, was reportedly attacked by BlackByte.
On April 13, Hertewing Noticias reported (machine translation), “The computer virus infected the national network, encrypting the documents and generating a payment request to recover them. It would have infected computer equipment of various delegations and subdirectories at the national level, encrypting all the files of the last fifteen years.“
No listing has appeared on BlackByte’s leak site, although screencaps provided in news coverage and on Twitter strongly indicate that this was a BlackByte attack.
Attempts to email Conagua on April 13 bounced back. A subsequent attempt to email them this morning did not bounce back, but no reply has been received as of publication.
Edited by Dissent