Schools continue to be an attractive and all-too-easy target for criminal groups. This week, Rhysida threat actors added Paris High School in Illinois to their leak site as an “auction” item:

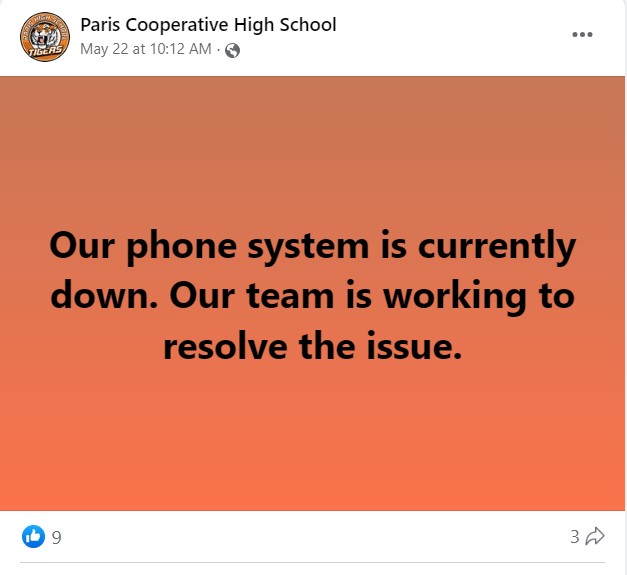
There is nothing on the district’s website to indicate any problems or breach. The only possible indicator currently found was on the district’s Facebook page in the form of a May 22 notice that their phone systems were down. There do not seem to be any follow-up posts to that although there were other posts about graduation and other normal activities.
DataBreaches notes that Rhysida appeared to offer some proof of claims as a collage of files and images from files that they presumably exfiltrated.