While LockBit was adding one physician-owned medical entity to its leak site, a relatively new group known as 8Base was adding another physician-owned medical entity to its own leak site.
8Base claims to have attacked Kansas Medical Center on June 18 and to have downloaded data on July 11. They claim they will publish the data as a leak on July 15.
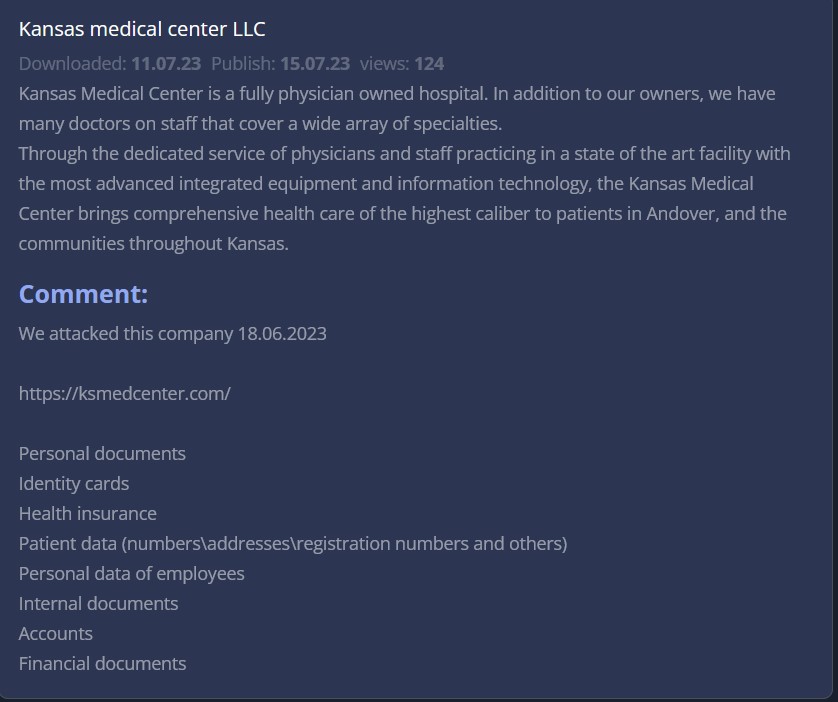
8Base does not indicate how much data it has acquired, but describes it as relating to:
- Personal documents
- Identity cards
- Health insurance
- Patient data (numbers\addresses\registration numbers and others)
- Personal data of employees
- Internal documents
- Accounts
- Financial documents
Unlike other ransomware groups that post proof of claims, 8Base does not seem to provide public proof that could be used to verify their claims. Finding no notice or any mention of a breach on Kansas Medical Center’s website, DataBreaches sent an email inquiry to the medical center earlier this morning, but no reply has been received by publication.