Coca-Cola FEMSA is the bottler of Coca-Cola and its related soft drink products in much of Latin America, which makes it an important part of the Coca-Cola system. This week, a threat actor known to DataBreaches as “TheSnake” and as the person who had also hacked a Brazilian clinic, leaked some data from Coca-Cola FEMSA on a popular hacking forum with a claim that they had acquired a “Full database Coca-Cola FEMSA containing company information, confidential photos and files, and much more.” They also posted a message to the company:
As we said, after the specified time, your data will be gradually uploaded to the public domain for everyone. You can still protect your reputation and keep most of the data undisclosed, but you have less and less time to do so. The choice is yours Coca-Cola FEMSA.
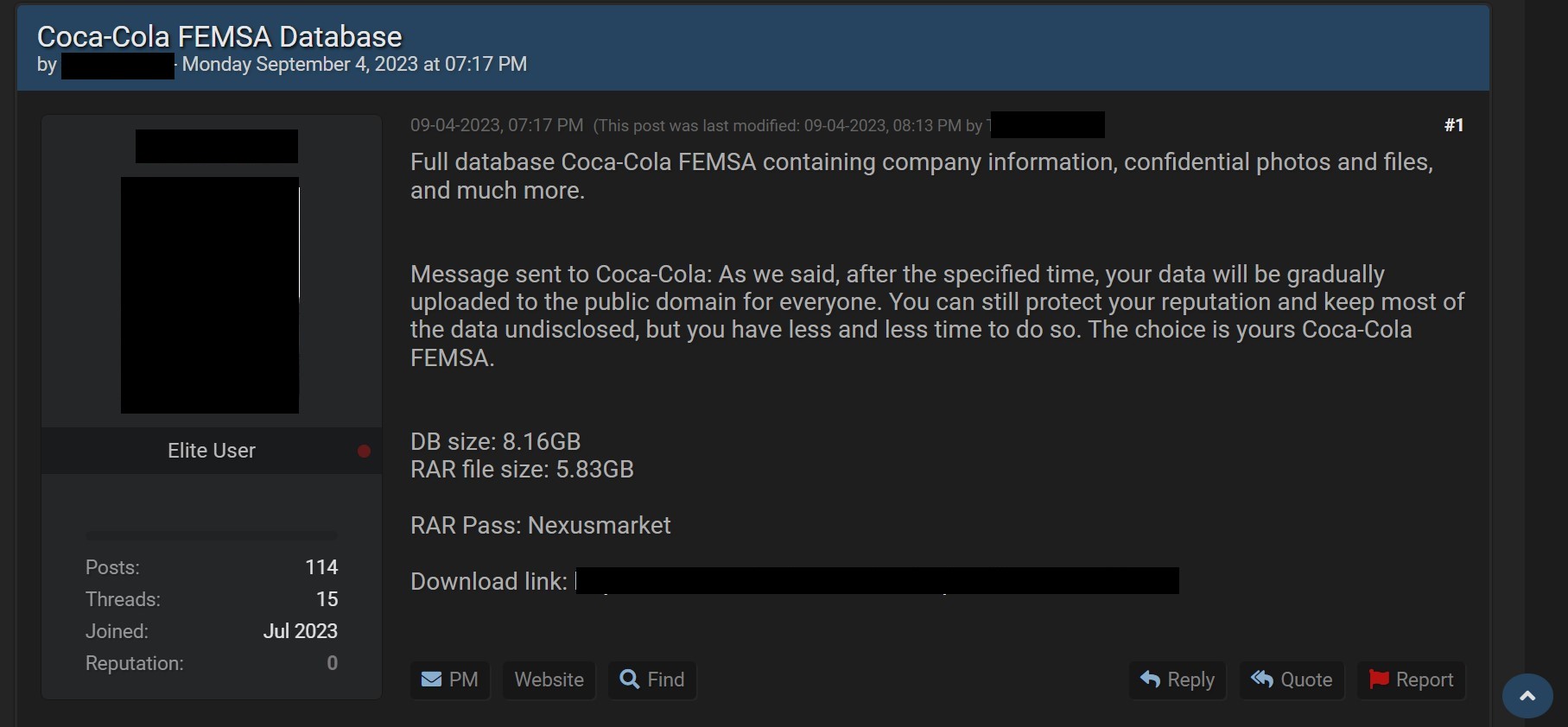
The listing indicated that the freely available data tranche was 8.16 GB in size, or 5.83 GB compressed.
TheSnake provided DataBreaches with additional details via an exchange of private messages. According to the information he provided, he was able to access Coca-Cola FEMSA twice in a period of a little over a year. The first time was in April 2022 and then again in June 2023. As before, they would not provide any statement about how they gained access, but did state that they had spent time researching their target and:
We had complete company information, including information from Mexico, Argentina, Brazil, Costa Rica, etc. The data had passwords, financial documents, invoices in ZIP and supplier data, data from facilities, company equipment, ad campaign, data and photos of employees, backups and much more, we had access to more than 200GB of company.
The attack involved both encrypting files and backups and exfiltrating data. TheSnake claims the encryption did not interfere with the firm’s functioning.
When asked whether the firm had responded to him at all or negotiated at all, he replied that the firm had reached out to “negotiate a fair agreement.” On inquiry, he clarified that they had demanded $12 million to delete all the files they had exfiltrated, but the firm was most concerned about preventing the leak of certain files and the negotiations were focused on a price not to leak those specific files. According to TheSnake, the company did pay them $1.5 million not to leak those files.
The rest of the files remained locked on their server. Now some of the exfiltrated files have been leaked freely. “If anyone is interested in the rest of the files, they are selling for US $65 thousand,” he added.
DataBreaches reached out to the firm via email yesterday evening to ask for a statement about the impact of the attack on their company. No reply has been received, however.
Update of September 9: Thanks to a sharp-eyed reader, DataBreaches learned today that AlphV (BlackCat) claimed responsibility for an attack on Coca-Cola FEMSA and leaked data from them on June 10. They used the same message to the company in their listing that TheSnake used.
In response to a question from this site when DataBreaches was looking into his listing, TheSnake had responded that he usually worked alone but had worked with a group on this attack. He never named the group or said anything about the attack being previously leaked online. Because his answer arrived after the post had appeared, DataBreaches didn’t think to follow up at that point.
DataBreaches was unable to connect to BlackCat’s downloads to determine if the leak was exactly the same as what TheSnake leaked. DataBreaches sent TheSnake an inquiry about the BlackCat listing and data. His reply complicated things even more, because he denied getting any data from AlphV. “I didn’t download it from this site. My work was together with Stormous,” he wrote to DataBreaches. “I don’t know how AlphV had access to this data either but they weren’t the ones who carried out the attack.”