Crystal Lake Health Centers (CLHC) provides comprehensive medical care in 11 healthcare clinics in Michigan.
On some date as yet unknown to DataBreaches, they appear to have been compromised by the Hunters International threat actors, who have since added a listing to their leak site. According to the leak site notice, Hunters acquired:
– patients data – employees data (contracts, contacts, ssn, address, etc) – financial data (budgets, cash flow, billing, payments, etc) – real estate data (statements, agreements, mortgage documents, taxes, etc) – insurance data (insurance virtual card number, contacts, CVV, valid thru, holder name, etc) – legal data (lawsuits, related docs, personal contacts, etc) – other sensitive data (info related to 2021 data breach, BOD meetings, BOD agendas, medical portals credentials, etc)
As proof, they have leaked 47.5 MB of data in 21 files. That is only a small portion of the 120 GB Hunters claims to have exfiltrated in total.
When Crystal Lake did not respond to Hunters, Hunters sent another email, a copy of which was shared with DataBreaches. It read, in part:
You have an opportunity to protect your business and keep this data leak incident confidential.
To do so you have to contact us and start negotiation process. Our experts will provide you with further details.
For a fee we will provide you with:
– network recovery tool
– network penetration test report
– data deletion log
– once you pay means that you will never see us and stolen data ever again
But in case if you will refuse to contact us we will deploy your data for public sharing.
Our contacts could be found within ContactUs.txt files. Or you can send email to redacted by DataBreaches
Have a nice day!
Sincerely yours, Hunters International Ransomware Team
DataBreaches examined the proof of claims files, and it does appear that Hunters has posted real data. A .csv file listed some patients’ information with more than 47,000 records with Last Name, First Name, Middle Initial, Birth Date, Street, City, State, Zip, Phone, and E-Mail. Other files contained sensitive personnel information such as disciplinary matters or performance concerns.
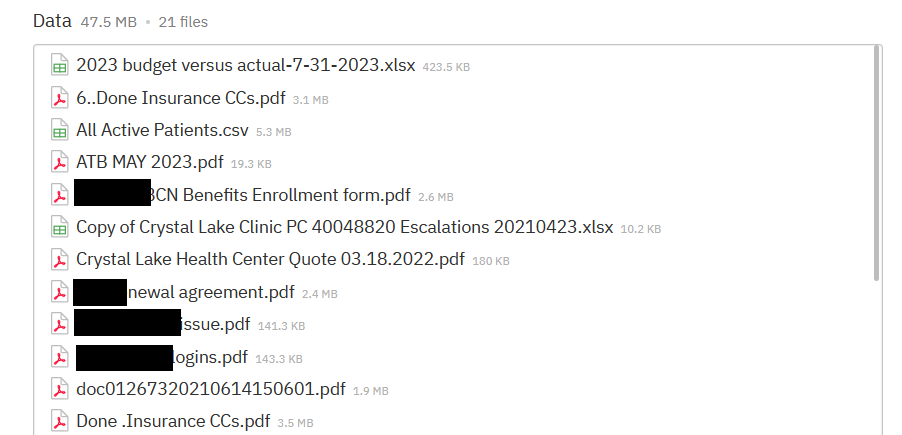 Partial listing of files leaked by Hunters International as proof of claims. Image and redaction: DataBreaches.net
Partial listing of files leaked by Hunters International as proof of claims. Image and redaction: DataBreaches.net
One of the files in the sample that DataBreaches viewed provided login credentials for a new employee. The login credentials were not only being reused across platforms and services, but were all fairly predictable and easily guessable combinations of name and year.
 Login credentials sent to a new employee appeared to be weak and reused credentials. Image and redaction: DataBreaches.net
Login credentials sent to a new employee appeared to be weak and reused credentials. Image and redaction: DataBreaches.net
DataBreaches sent an email inquiry to Crystal Lake asking for a statement about the attack and their incident response. No reply has been received.
The countdown clock on Hunters International leak site indicates that CLHC has two more days to respond before the threat actors would presumably leak more, or all, of the 137.6 GB of files (37,260 files) the site claims to have.
DataBreaches will continue to monitor this listing and will update this post when more information becomes available.