United Urology Group describes itself as a national network of urology specialists with corporate headquarters in Maryland. Their network includes Arizona Urology Specialists Phoenix, Arizona Urology Specialists Tucson, Chesapeake Urology, Colorado Urology, and Tennessee Urology.
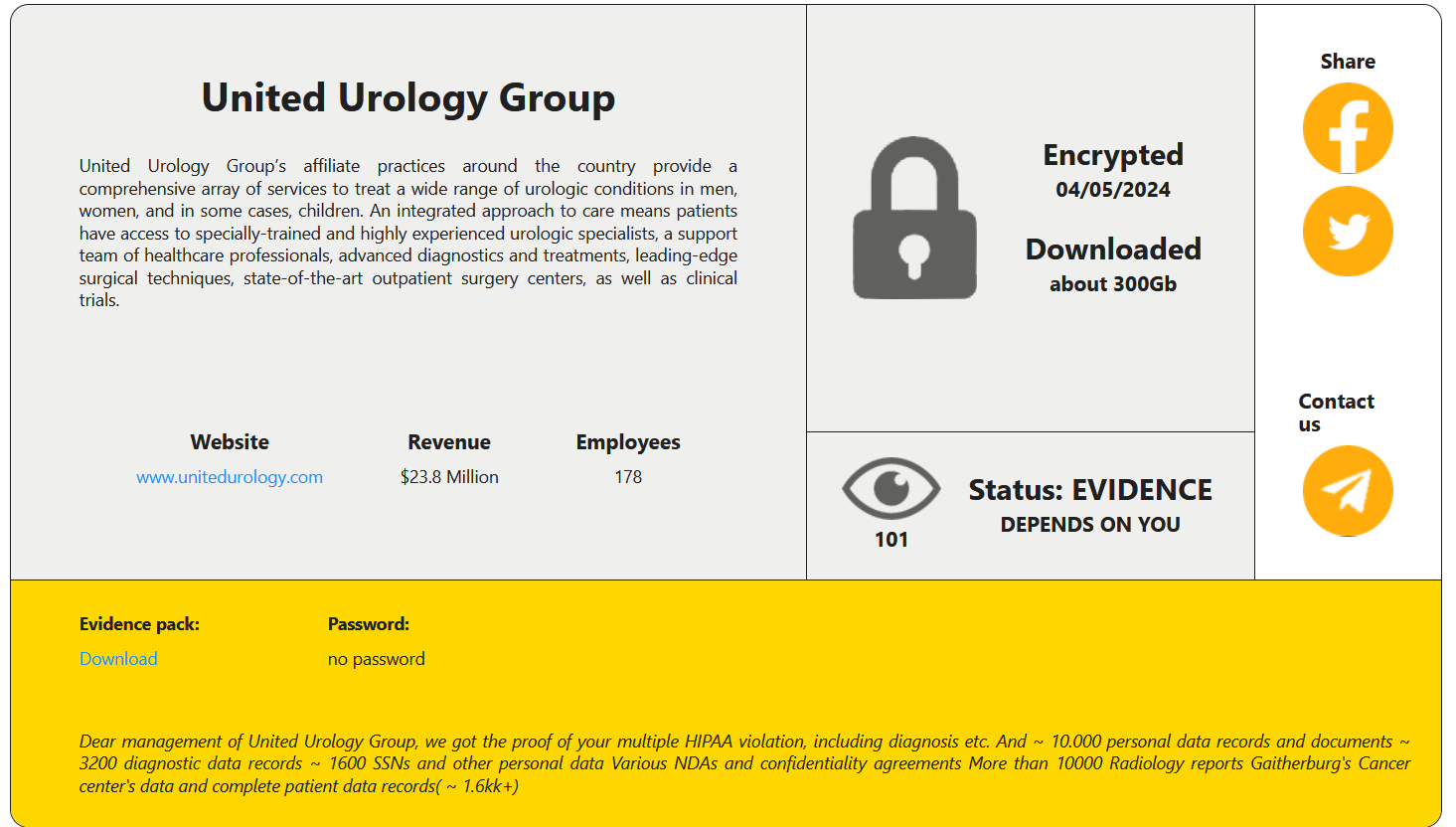
On May 23, RansomHouse threat actors claimed to have encrypted their system on May 4 and exfiltrated about 300 GB of files.
RansomHouse’s listing includes a note:
Dear management of Urology Group, we got the proof of your multiple HIPAA violation, including diagnosis etc. And ~ 10.000 personal data records and documents ~ 3200 diagnostic data records ~ 1600 SSNs and other personal data Various NDAs and confidentiality agreements More than 10000 Radiology reports Gaitherburg’s Cancer center’s data and complete patient data records( ~ 1.6kk+)
Data Tranche
While DataBreaches cannot confirm all of their claims, an inspection of parts of a data tranche provided as proof of claims did reveal many files with protected health information (PHI). In one directory alone, there were numerous radiology reports on named patients. Other files contained other PHI and PII such as reports on diagnoses and pictures of driver’s licenses.
Some files contained corporate internal information. DataBreaches noted files that contained logins and passwords that appeared to be recent. DataBreaches did not test any of the credentials to determine if they were still working but noted that even security questions and answers were included for one employee.
Although DataBreaches did find some confirmation for some of RansomHouse’s claims about types of information, their “multiple HIPAA violation” allegation seemed a bit of an exaggeration. DataBreaches’ inspection of files found that United Urology Group logs all incidents that get reported to HHS as part of an “under 500 affected” report each year. There was nothing that DataBreaches saw that seemed particularly unusual or noteworthy. Although any breach — including a single mismailing of patient info — is not desirable and is reportable, these things do happen.
There is no notice on United Urology Group’s website as yet. DataBreaches emailed two United Urology Group executives to ask what UUG is doing in response to the breach and whether they have already disabled all the leaked login credentials. No reply has been received by publication, but RansomHouse did respond to an inquiry asking whether there had been any negotiations between them and UUG. They responded that there had been no negotiations.