On June 12, BreachForums reappeared on clearnet and Tor. The owner — or someone with access to the forum owner’s account — interacted a bit in the ShoutBox and posted an announcement:
Hello BreachForums users!
Some wild stuff has gone down recently. First off, Spamhaus has blacklisted our SMTP host. Then, we ran into more issues with our NGINX config. To top it off, our Telegram account (@shinycorp) and the “Jacuzzi 2.0” group got banned and blacklisted. Because of all this, we’re stepping away from using any Telegram account for ShinyHunters, and honestly, it’s kind of sapped our motivation to keep the forum going, though we’ll keep it alive. If you have any questions about rank, escrow, or anything else, hit up @Hollow (likely the next owner). Also, the canary has been updated.
PGP: https://pastebin.com/raw/qUp9Ax9M
PGP Archive Link: https://web.archive.org/web/202109211113…inyHunters
While many were glad to see the site back, ShinyHunters’s announcement claimed that they had lost motivation to keep the site going given all the hassles, and that a current moderator might be the next owner.
But was that really ShinyHunters? Is the forum now a honeypot?
DataBreaches received an interesting note this morning from a reader:
shiny php dismatched his newly signed canary
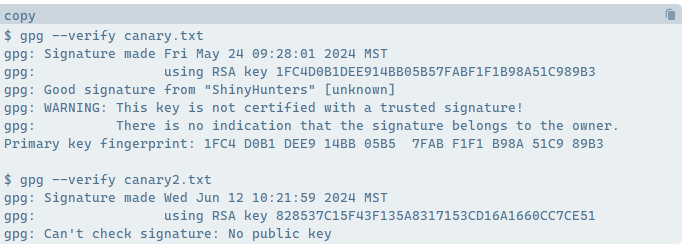
surely a honeypot now$ gpg –verify canary.txt
gpg: Signature made Fri May 24 09:28:01 2024 MST
gpg: using RSA key 1FC4D0B1DEE914BB05B57FABF1F1B98A51C989B3
gpg: Good signature from “ShinyHunters” [unknown]
gpg: WARNING: This key is not certified with a trusted signature!
gpg: There is no indication that the signature belongs to the owner.
Primary key fingerprint: 1FC4 D0B1 DEE9 14BB 05B5 7FAB F1F1 B98A 51C9 89B3$ gpg –verify canary2.txt
gpg: Signature made Wed Jun 12 10:21:59 2024 MST
gpg: using RSA key 828537C15F43F135A8317153CD16A1660CC7CE51
gpg: Can’t check signature: No public keycanary.txt is the older canary from 5/24
canary2.txt is the new canary from 6/12 and DOES NOT MATCH
ShinyHunters: Get in Touch
@ShinyCorp: if you happen to read this post, please get in touch.
Update
When a forum user posted about the issue of the mismatch, ShinyHunters responded:
Yes, it’s a mistake from @Hollow
I’ll put my PGP back and we’ll announce a common Staff PGP later.PGP: https://pastebin.com/raw/qUp9Ax9M
PGP Archive Link: https://web.archive.org/web/202109211113…inyHunters