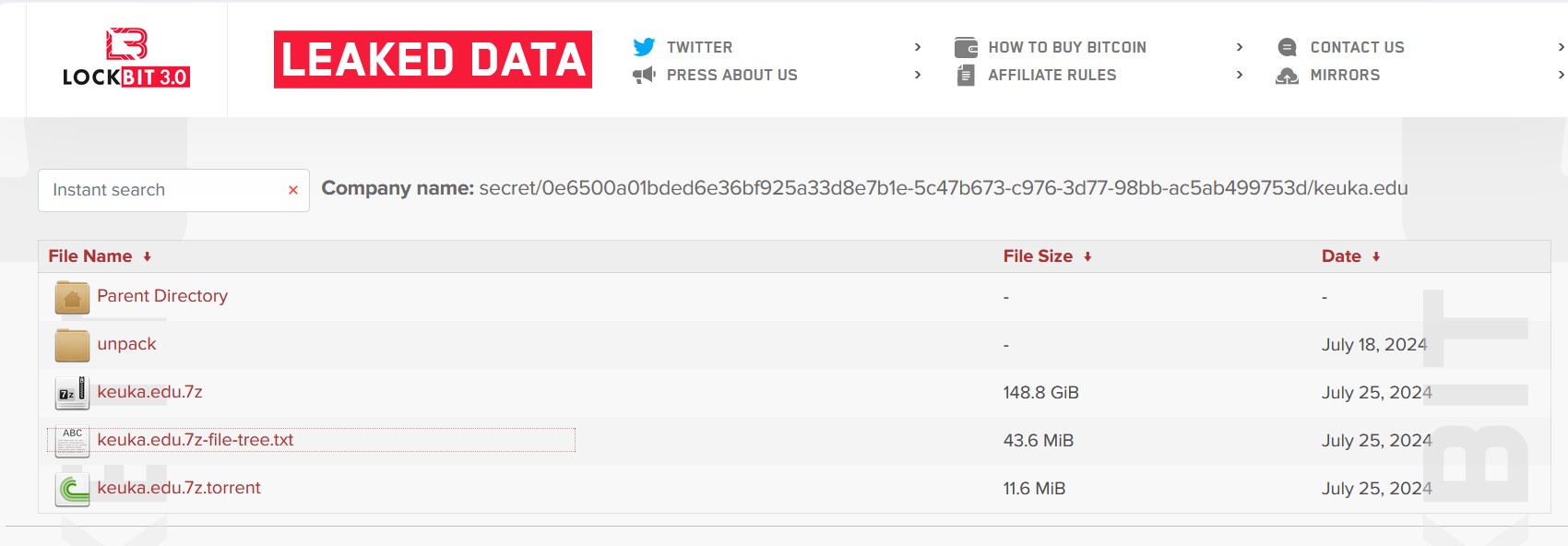
Note: The following press release from Keuka College does not mention that this attack was claimed by LockBit in May and added to LockBit’s leak site in August.
Sept. 20, 2024 /PRNewswire/ — Keuka College has learned of a data security incident that may have involved personal information.
On April 25, 2024, the College identified suspicious activity within its network environment and immediately took steps to secure the environment, restore its systems, and began an investigation to determine the nature and scope of the issue. Keuka College also engaged independent cybersecurity specialists to assist with the process. The comprehensive investigation, which concluded on August 21, 2024, could not determine definitively whether personal information related to current and former students and employees was affected.
Keuka College maintains a variety of records which can include: name, Social Security number, Driver’s license number, student id number, financial account information, and date of birth. Current students and employees were contacted by the College in May and provided with one year of free credit and identity monitoring services.
Keuka College has established a toll-free call center to answer questions about the incident and address related concerns. Call center representatives are available Monday through Friday from 9:00 am to 9:00 pm Eastern Time and can be reached at 1-833-913-7557. Please be prepared to provide the engagement number, B131983, for reference.
SOURCE Keuka College
Comment
The press release states, “The comprehensive investigation, which concluded on August 21, 2024, could not determine definitively whether personal information related to current and former students and employees was affected.” Why? On May 15, 2024, LockBit3.0 added Keuka to its leak site with some proof of claims. On August 11, 2024, LockBit updated its site. LockBit posted a file tree. They also leaked 148 GB of files. Both were date-stamped July 25, 2024 and leaked on LockBit’s leak site in August.
Did the “comprehensive investigation” conclude without specialists and investigators downloading and examining the data tranche to determine if personal information was in there? Why did they “conclude” any investigation if it was clear LockBit had dumped data or was likely to?