Several days ago, Cybernews claimed “exclusive research” that they headlined by claiming, “One-third of the US population’s background info is now public.” DataBreaches pointed out that their reporting was missing important details. DataBreaches wrote:
Unfortunately, they fail to clearly report when they discovered the leak, whether or when they contacted the entity to alert them to the leak, and whether and how the entity responded. Has this leak been secured? One certainly hopes so but their headline says the info is now public — as in still publicly available? One hopes not.
Today, I was reminded that their “exclusive research” wasn’t exclusive at all because someone else had not only discovered the same leak, but had taken the time and trouble to get it closed down and reported on it all before Cybernews reported what they called their exclusive research.
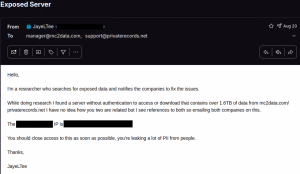
Here is the post from researcher JayeLTee on infosec.exchange on September 4:
US Data broker selling reports based on “public” records exposes databases with over 1.5TB of their own data publicly
On August 18th I got an alert for a server with over 1.5TB of data exposed. The next day I checked what this server contained and after checking some of the tables I started looking at who owned this so I could contact them.
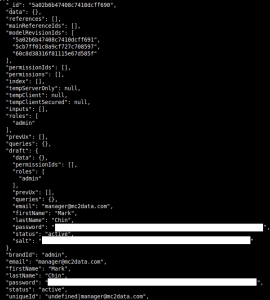
Initially on my search I could see a lot of links to https://www.privaterecords.net/ but when I started looking at the user table, things got confusing. The initial admin accounts all belonged to @mc2data.com emails. Searching the company name I could find the owner’s LinkedIn but the website didn’t load for me and I couldn’t find anything else on them. I could also see each user was linked to a brand ID(name) and I could see 15 different brands (websites) that sell reports on public data, all similar to each other linked to each user. I don’t know if mc2data owns all these websites or what’s the connection, but I’ll list them all at the end and you can check them and see how they all look oddly similar.
For the contents inside of this server:
– User table with 2.3 million users, with first and last name, email, hashed passwords, plaintext credit card information (at least type, last 4 and expiry date), zip codes
– Over 100 million entries for people’s search info, some of which contained a wild amount of information (I saw entries with over 50 criminal records linked to 1 person) such as full names, previous and current addresses, neighbours and relatives data. SSN was also present in a lot of these results, the ones I checked had the last 4 digits of it missing, but I can’t confirm if that was the case for every SSN entry on this.
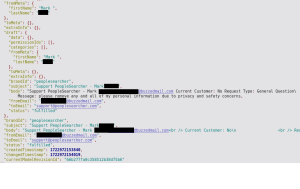
– Over 1 million notes that sometimes contained messages sent by their clients for updates, refunds, etc
– Over 200,000 emails sent to support of the various websites listed below
– Millions of entries for various types of tracking data they collect from their websites
I cannot verify if the data inside this was 100% accurate, but checking privaterecords.net reviews online they do seem to give a lot of wrong information on their lookups and a lot of people claim to have been charged by the website but never used it. Scamadviser has a Trustscore of 1 out of 100 for privaterecords.net.
On August 20th I contacted [email protected] and privaterecords.net support email and within a few hours this server was closed, I never got a reply from anyone on this though. I don’t know how long or if anyone grabbed the data while this was exposed.
The websites linked in this server:
https://www.privaterecords.net/
https://www.backgroundcheckers.net/
https://www.checksecrets.com/
https://www.inmatessearcher.com/
https://www.mugshotlook.com/
https://www.peoplesearch123.com/
https://www.peoplesearcher.com/
https://www.peoplesearchusa.org/
https://www.personsearchers.com/
https://www.privatereports.com/
https://www.publicsearcher.com/
https://www.sealedrecords.net/
https://www.secretinfo.org/
https://www.truthrecord.org/
https://www.weinform.org/Either a lot of data scientists and engineers decided to band together and build different but oddly similar websites or maybe these are all owned by the same person/company, I can’t confirm any of it though.

Today, Cybernews updated its original story to include more details, but it seems almost certain that JayeLTee’s efforts resulted in the data being secured.