On September 7, RansomHub added Cardiology of Virginia to its dark web leak site, claiming that about 1 TB of files had been acquired. DataBreaches assumes no payment agreement was struck as RansomHub subsequently leaked data, complete with a filelisting, youtube video, and other files.
“For bulk archive and confidential data analyzes trough our own private AI contact us trough TOX,” they wrote when they leaked the data.
Spelling errors aside, DataBreaches was intrigued by the offer of their own private AI to generate data analyses. This site has reached out to RansomHub to inquire about those services, and hopes they will respond. But there’s more to the data leak part of this story.
On October 11, the data from that attack was put up for sale on BreachForums. The seller, “RADAR,” provided the same file list and other proof of claims that RansomHub had posted.
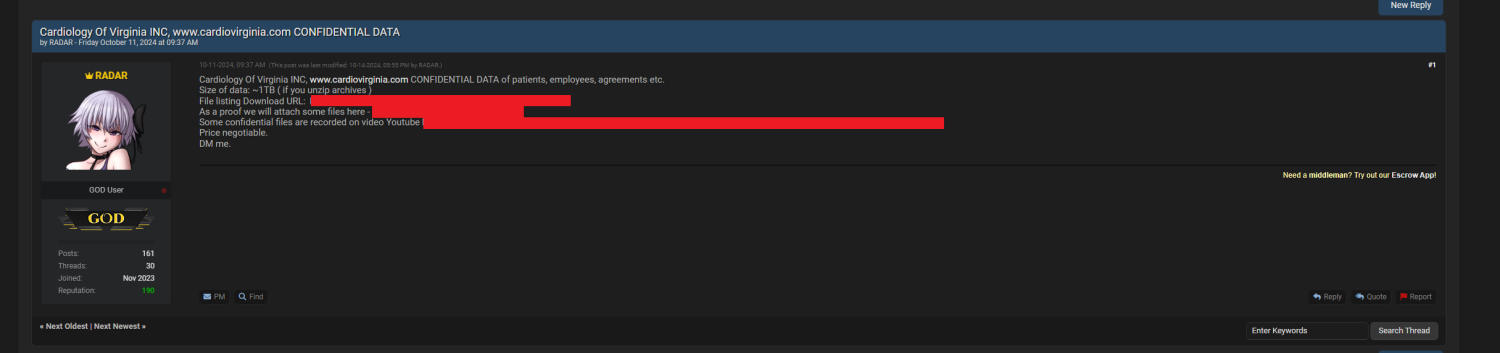
Radar’s listing did not indicate a price, and instructed potential buyers to contact them via DM on the forum.
But was Radar selling the same data that RansomHub already freely leaked, or had RansomHub leaked only some of the data, and Radar was attempting to sell all of it? Were they working together?
DataBreaches reached out to both Radar and RansomHub to inquire, but no replies have been received as yet.
What Has Cardiology of Virginia Done?
It is not clear what Cardiology of Virginia has done in response to what appears to be a reportable HIPAA breach. There is nothing on their website confirming or denying any breach, and DataBreaches was unable to find any press release or report to any regulator. While HIPAA’s notification deadline of 60 days from discovery has not run out yet, the absence of any public disclosure when data has already been leaked and is up for sale may result in the patients being the last to find out that their information has been stolen and leaked.
Given how quickly some stolen data can be misused, the patients need to be informed so they can take steps to protect themselves, but DataBreaches has been unable to find any evidence that they have been notified.
DataBreaches sent an inquiry today to Cardiology of Virginia this morning, seeking a statement about what they have done in response to this incident. No reply has been received as yet.
This post will be updated if more information becomes available.
