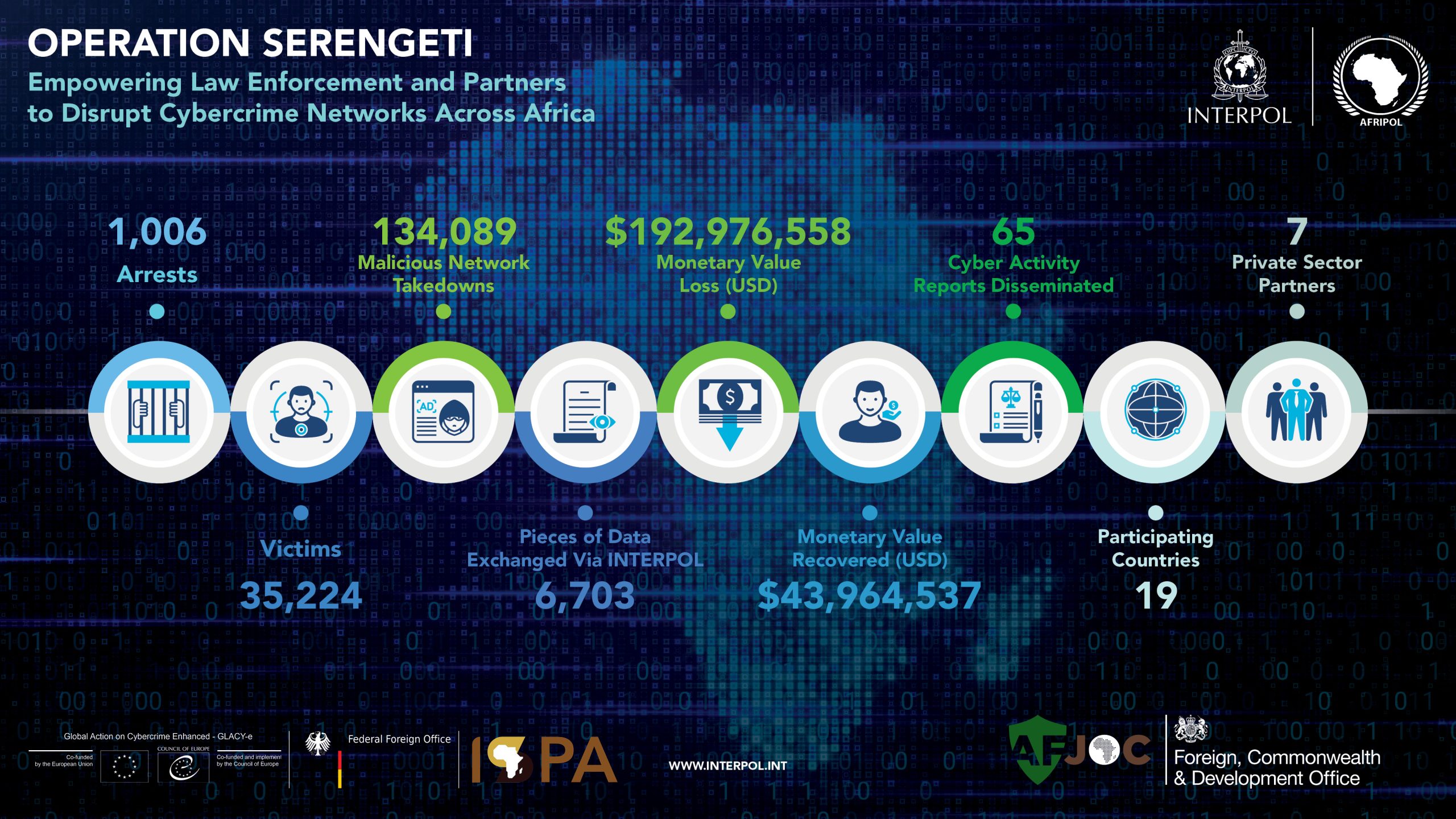
LYON, France – Authorities across 19 African countries have arrested 1,006 suspects and dismantled 134,089 malicious infrastructures and networks thanks to a joint operation by INTERPOL and AFRIPOL against cybercrime.
Operation Serengeti (2 September – 31 October) targeted criminals behind ransomware, business email compromise (BEC), digital extortion and online scams – all identified as prominent threats in the 2024 Africa Cyber Threat Assessment Report.
More than 35,000 victims were identified during the operation, with cases linked to nearly USD 193 million in financial losses worldwide.
Information provided by participating countries of ongoing cases with INTERPOL fed into 65 Cyber Analytical Reports that were produced to ensure actions on the ground were intelligence-led and focused on the most significant actors.
Read more at Interpol. Interpol notes its Operational Partners: Cybercrime Atlas, Fortinet, Group-IB, Kaspersky, Team Cymru, Trend Micro, Uppsala Security
Source: Interpol