Threat actors’ leak site unreachable due to DoS attack; DataBreaches given exclusive preview of leak
Marc Fortier reports:
The hackers behind a major cyberattack that hit the State of Rhode Island’s online system for delivering health and human service benefits have released some residents’ files to a site on the dark web, state officials announced Monday.
“Unfortunately, Deloitte has informed us that the cybercriminal released at least some RIBridges files to a site on the dark web,” a release from Gov. Dan McKee’s office said. “This is a scenario that the State has been preparing for, which is why earlier this month we launched a statewide outreach strategy to encourage potentially impacted Rhode Islanders to protect their personal information.”
They said IT teams are working to analyze the released files, and while they don’t yet know the scope of the data included in those files, they are assuming that data contained in the RIBridges system has been compromised.
Read more at NECN. The subsequent press conference this afternoon did not add any additional details.
When Deloitte did not reply to previous inquiries from DataBreaches, this site reached out to Brain Cipher, the threat actors responsible for the attack. They confirmed that they were responsible for the attacks, and gave DataBreaches an exclusive preview of the data they would be releasing.
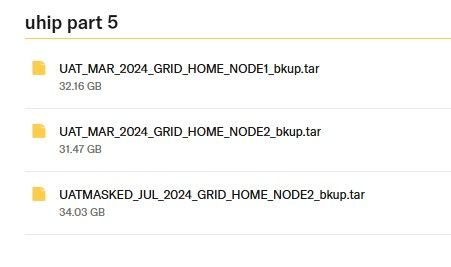
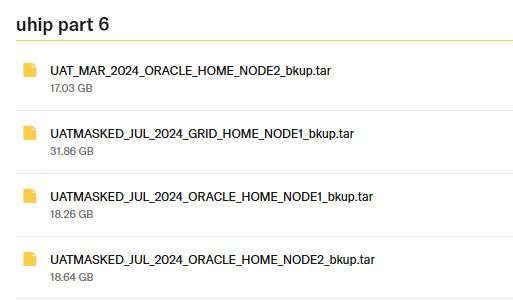
DataBreaches has not downloaded all the data or analyzed it, but did inspect the RIKids-SSA[.]zip archive and found a lot of personal information in it. DataBreaches is not leaking the data, but is showing the directories of files involved. The state has said that it does not yet know the scope of the breach and that Deloitte is investigating.
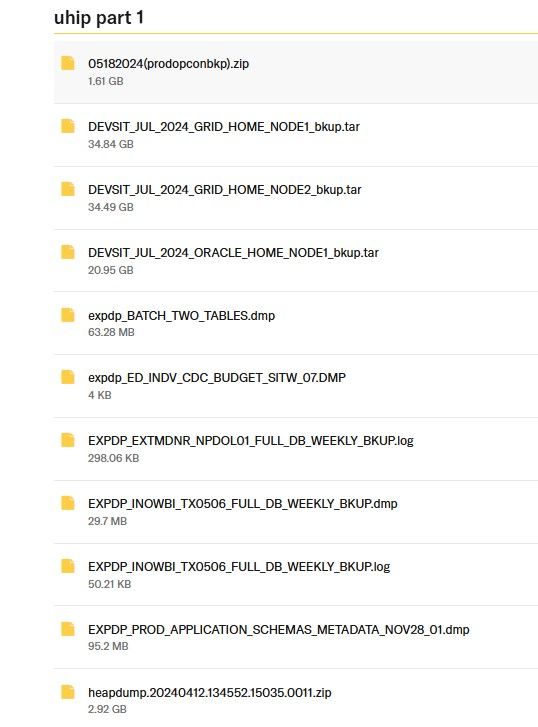 |
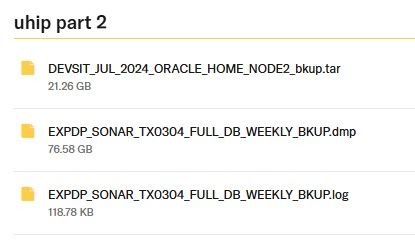 |
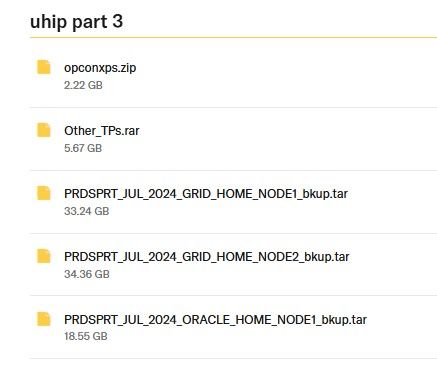 |
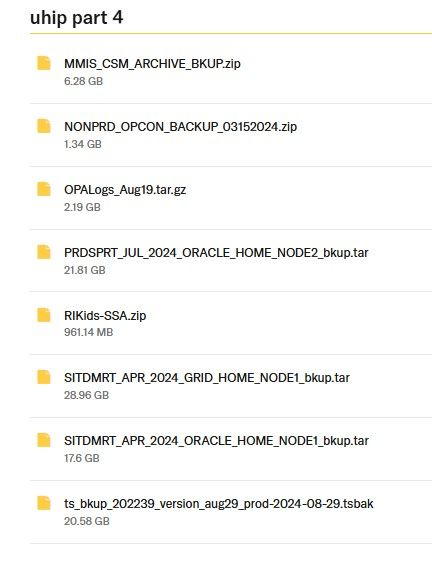 |
 |
 |
DataBreaches also reached out to Deloitte yesterday to inform them that this site has been given access to a large tranche of the data from Rhode Island and that the threat actors inform this site that they will be providing more information after they leak the data. Whether Deloitte’s alert to the state this morning that data had been leaked on the dark web is related to DataBreaches’ email to them yesterday is unknown to DataBreaches at this time.
Deloitte did not reply to a request for a statement about what they are doing in response to the incident.
At the present time, it is has been actually impossible, if not difficult, to reach the threat actors’ dark web leak site. Brain Cipher’s spokesperson stated that they have been under DoS attack, which they attribute to someone trying to stop them from leaking data.
A quote from NECN was corrected post-publication after it was discovered that the sentence had been broken up in transposing it.
