Felix Cortez reports:
Just months after Watsonville Community Hospital was hit by a cyber-attack, roughly 20 employees at the hospital now say they’re the victims of identity theft.
“We heard from a few of our employees that they reported there were fraudulent tax filings in their name, so someone else had tried to file a tax return in their name and they had received that notification from the IRS,” said hospital spokeswoman, Nancy Gere.
One employee who didn’t want to be identified told Action News 8 she had not yet filed a return but when she signed onto her IRS account it showed an $8,000 refund being processed she added the refund was flagged by IRS agents and not disbursed.
Coincidentally, DataBreaches had reached out to the hospital earlier this week to ask about any update because the incident still doesn’t appear on HHS’s public breach tool months after the incident was discovered.
But let’s back up a bit.
Watsonville Community Hospital first disclosed that they were dealing with a a cyberattack on November 29, 2024. In a substitute notice posted on December 31, 2024, they noted that patients’ name, date of birth, Social Security number, passport number, and diagnosis information may have been present in files that had been accessed in a “recent data security event” that was still under investigation. They did not confirm or deny whether this was a ransomware attack.
Although individual notification of those affected had not yet taken place, threat actors known as Termite added the hospital to its dark web leak site on December 11. Watsonville may not have described the incident as a ransomware attack, but intel firms reporting on Termite at the time described it as a ransomware group using an older version of Babuk ransomware.
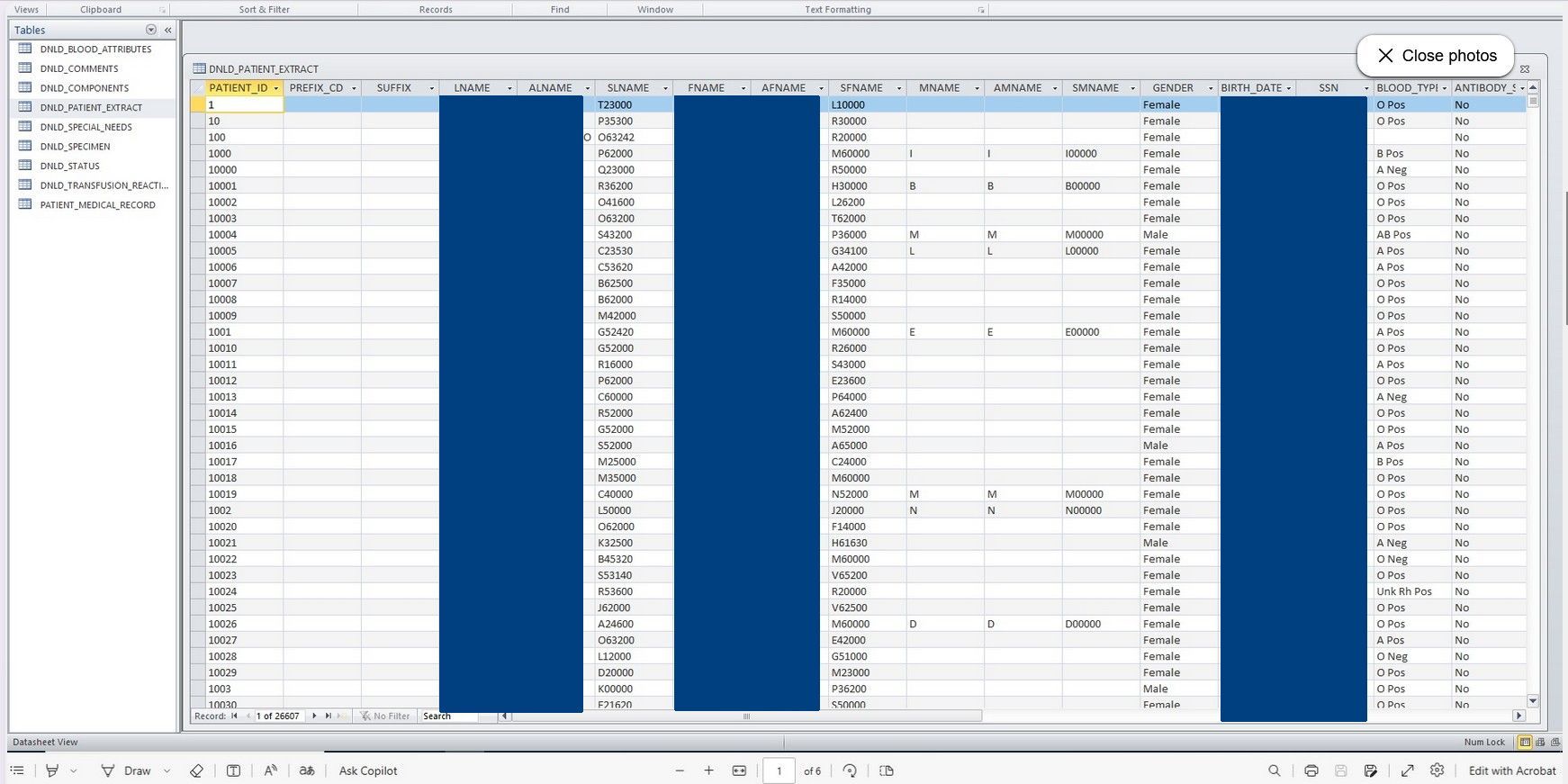
Termite’s leak site was last updated on January 8, 2025. The proof of claims included screenshots from what appears to be a very sensitive personnel-related file as well as screenshots of a patient-related file and a patient-related spreadsheet (below).
So who has actually been notified by now? Did any of the employees receive individual notification letters? Did any patients?
If the hospital has not complied with state and HIPAA requirements to notify timely, why haven’t they been able to comply?
Watsonville did not respond to the inquiries emailed to it on March 18, and Termite does not list any way to contact them with questions. If they happen to see this post, perhaps they will get in touch as DataBreaches has some questions for them, too.
But will employees be able to demonstrate that this incident was the source of their identity data that was used for fraudulent tax filings? If it was only one or two employees, it might be difficult to demonstrate the link, but if 20 employees or more are all reporting tax refund fraud, then that makes it more likely that the incident was the common point of compromise, although it is still a question that will likely be raised in any litigation.