A notice on St. Cloud, Florida’s website:
May 29, 2025 – The City of St. Cloud, Florida (the “City”) is issuing updated notice of an event that may impact the security of information related to certain individuals. This notice supplements the notice previously posted on or website on or about May 24, 2024.
What Happened? On or about March 25, 2024, the City became aware of suspicious activity in its computer environment. We promptly took steps to secure our systems and launched an investigation, with the assistance of third-party cybersecurity specialists, to determine the nature and scope of the event. The investigation determined that between March 17, 2024 and March 25, 2024, an unauthorized actor gained access to certain systems and obtained certain information. In response, we undertook a comprehensive review to determine what information was involved and to whom such information relates, as well as to confirm the identities of, and appropriate contact information for, those potentially impacted. We recently completed this process and then moved as quickly as possible to provide notice.
What Information Was Involved? The types of information potentially impacted vary by individual and could have included: full name, address, Social Security number, date of birth, driver’s license number or state identification number, Passport number, taxpayer identification number, U.S. military identification number, United States alien registration number or other government identification number, taxpayer/international taxpayer identification number, employer identification number, employer assigned identification number, financial account information, payment card information, online account login credentials, medical information, and health insurance information.
Read more on the city’s website.
On May 24, 2024, the city, in its capacity as a health plan, notified HHS of the attack, but only used a “501” as a placeholder for the number affected. As of publication today, that number has never been updated.
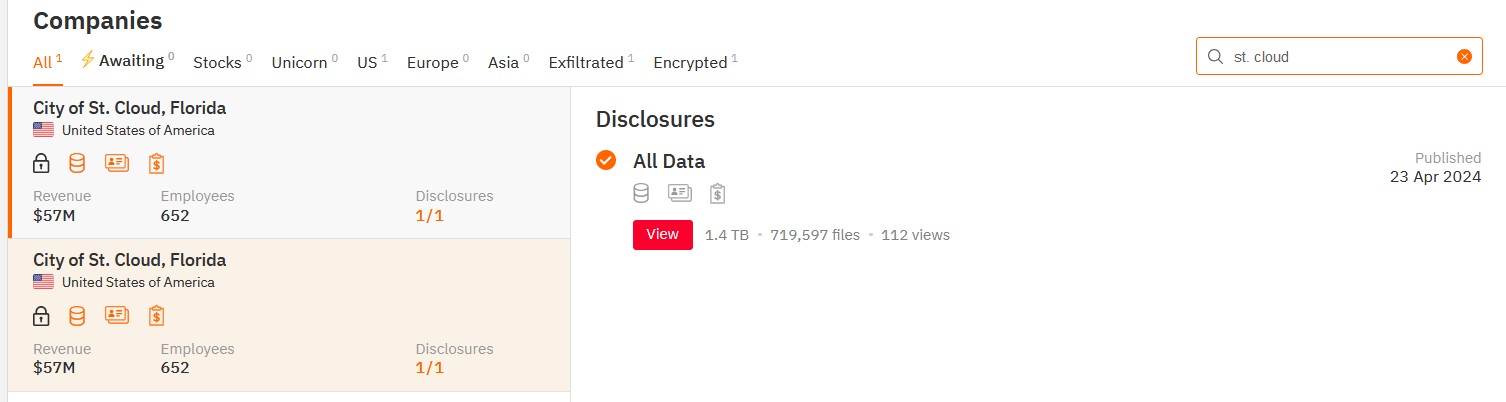
Although the city’s notice does not specifically mention “ransomware” or any data leak, the city police confirmed it was a ransomware attack. In April, 2024, the Hunters International ransomware gang claimed responsibility for the attack and encryption, and later leaked what they claimed was 1.4 TB of data consisting of 719,597 files. While the listing is still viewable on the dark web, the links to data do not work.