On October 5, Salud Family Health in Colorado notified HHS of a breach, but only provided a “marker” of 501 affected. On November 4, they provided notice that said the types of information that might have been accessed or taken included in a cyberattack included: patients’ name, Social Security number, driver’s license number or Colorado identification card number, financial account information/credit card number, passport number, medical treatment and diagnosis information, health insurance information, biometric data, and username and password. A notice also appears on their website.
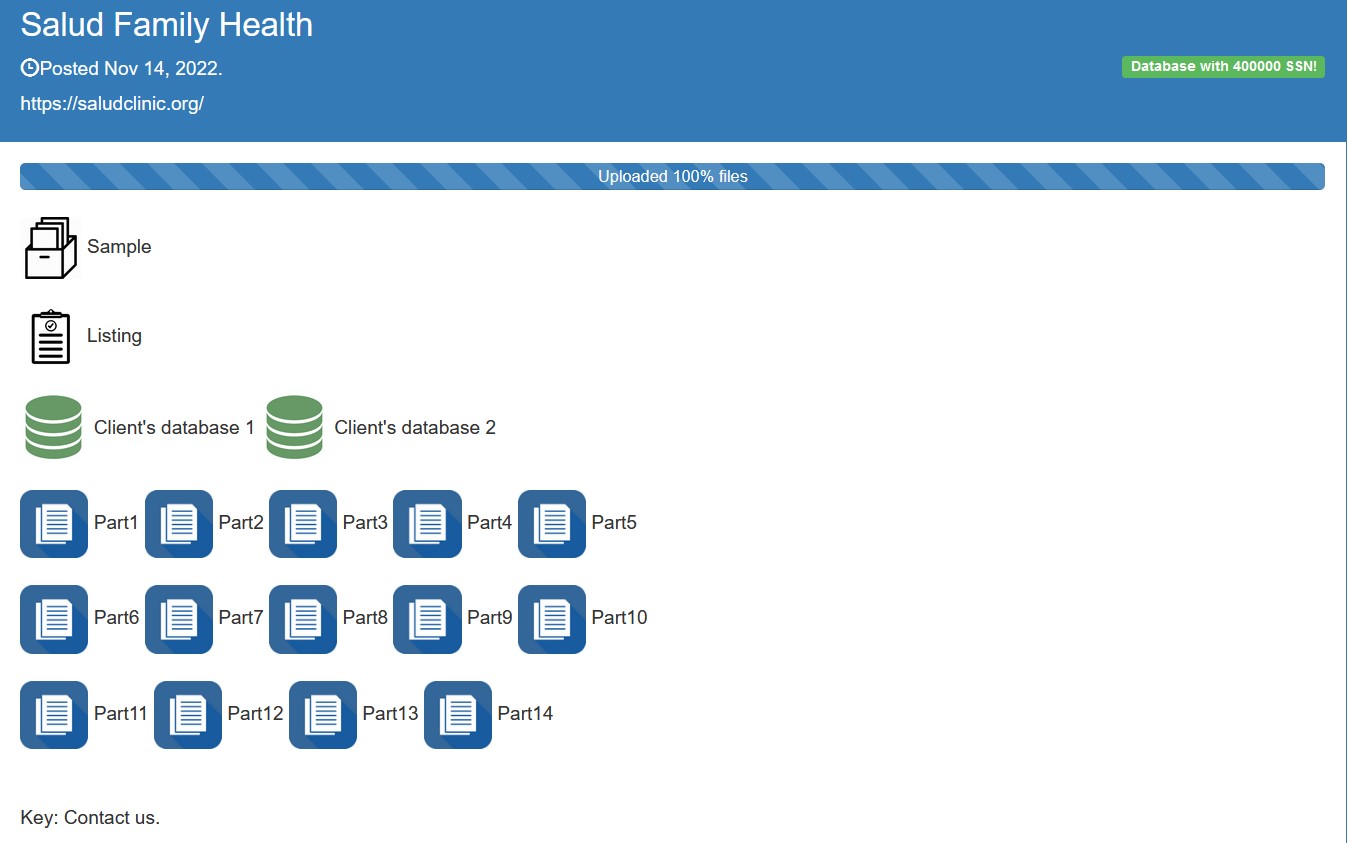
Salud’s statement that patient information “may have been accessed or taken” seems a bit mild in light of the fact that the threat actors have now dumped data and claim to have about 400,000 social security numbers. While the databases and bulk of the data cannot be viewed without a password, Lorenz has made a file list and a small sample of files available as proof.